 Giacomo Lanzi
Giacomo Lanzi
cPanel and Plesk the best for hosting management
Most hosting environments use an intuitive interface to help users manage their web spaces. Two very famous panels are cPanel and Plesk, widely used and offered in the SaaS formula. Without these graphical interfaces, it would be difficult to manage a hosting space and set up a site. A lot of time is usually spent managing a web space through a control panel, consequently, the choice of a provider should also be made based on the panel it offers, how user friendly it is and what features are immediately available.
Let’s see what are the generic advantages of a web panel and try to understand why the use of a product like Plesk is to be preferred.
Why use a web panel?
A web panel is essentially a hosting management tool. It allows you to do things like organize site files, manage installed applications, email and much more. Providers offer a panel to help their customers effectively manage their sites. Without such a dashboard, managing a web portal and server would be much more complicated and would require a lot of additional skills.
The great advantage of control panels is that they allow users to set up and manage complicated processes with the click of a button.
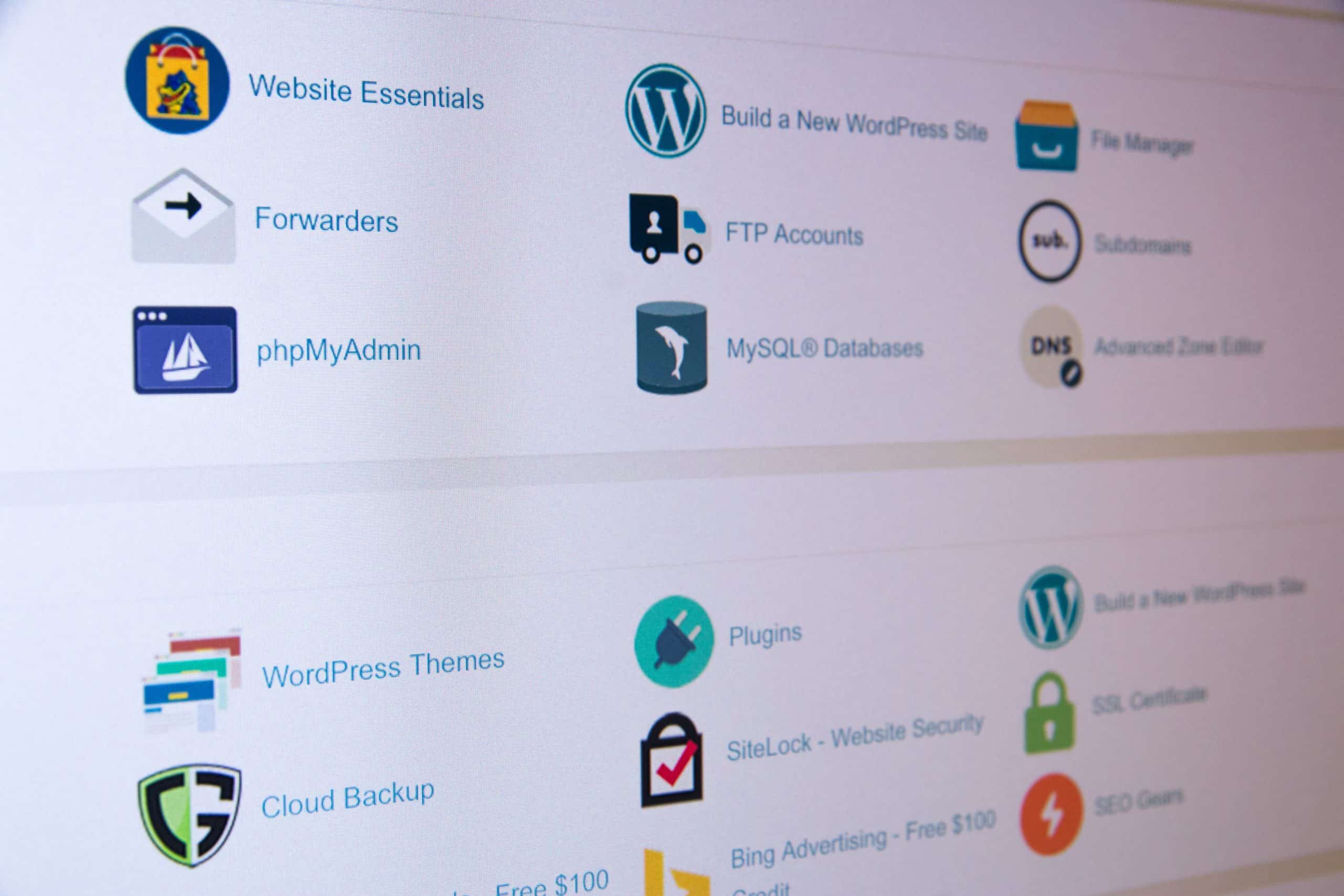
Some things that can be done simply with a click: install a CMS, generate a subdomain, install software on the server and much more. All this is just the tip of the iceberg of what a panel like cPanel or Plesk can do.
Common features of web panels
Regardless of which web panel you end up using, you will likely have access to a similar set of functions. Below we take a look at what these features are.
DNS management
DNS is the acronym for domain name management system. Most web panels provide the tools you need to manage domains, connect them to an existing site, redirect domains, and much more.
File and database management
These features allow you to manage the files of your web space through the cPanel and Plesk panels. With the management via FTP it will be possible to access the single files of the site, in some cases directly from the panel, and to modify them as desired. The database management offers the same editing function for the tables and the data contained within it. It may not be necessary to use these features often, but they are essential to have full control of your site.
Email management
Having an email address associated with the domain name helps the site look professional. With the e-mail management functions you are able to set a specific e-mail address for the domain, send and receive e-mails and other operations related to messaging.
Backup management
The backup of the web portal is incredibly important for the security of your data. it is a great way to help mitigate risks in case the site is hacked, or if there is a problem blocking the site. With a regular backup system, it is easy to restore a previous version of the site in case of need.
Installation of applications and software
Most control panels have various software and applications that can be installed with just one click. One of the most common uses is to allow you to install popular software like Joomla !, or WordPress, with the click of a button.
Why choose cPanel or Plesk
If it is true that web panels often offer similar functionalities, the solutions to offer a user interface to their customers are different and can be divided into two broad categories: providers who rely on services such as cPanel or Plesk, and those who instead use a customized panel with all the resulting risks.
The choice of a control panel developed by companies specialized in the service is a safety in terms of stability, support and potential. Products like the ones we are about to describe have years of experience behind them, large communities and many users who can guarantee that every problem is identified and solved in the shortest possible time.
These obvious benefits are not available on custom web panels or developed directly by service providers to save money. When it comes to the security and stability of your site, don’t take any chances.
cPanel
it is one of the most popular panels and one of the most used, although only available for Linux servers. Its features include both an interface for the end user and one for managing the server via WHM. It is also possible to expand its functionality with additional packages.
cPanel is one of the most popular web panels available today. With its wide variety of features, intuitive interface and extensive customization options it has been designed to meet a broad spectrum of hosting needs.
Plesk
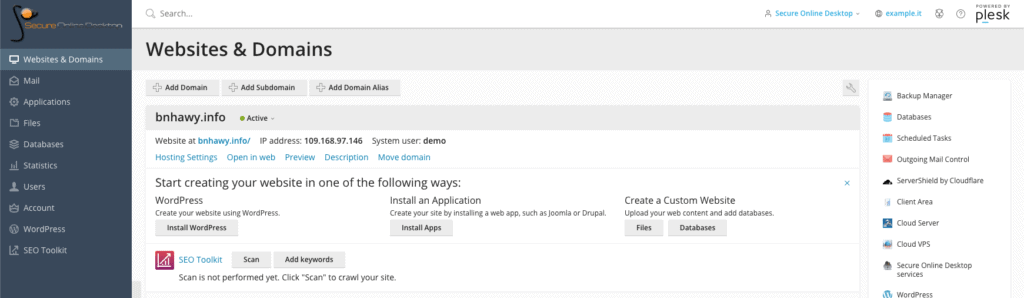
Plesk is available for both Linux and Windows environments. it is one of the easiest to use control panels available for the Windows hosting environment. It offers a very clean user interface and multiple product options to suit different hosting environments. It also allows the management of access by the end user.
Plesk is also the panel in use in our web hosting service. Try the panel with the free demo!
Its intuitive graphical interface is designed to eliminate the hard work of managing the host. It offers a suite of tools to improve the security of your site and the development environment in general. A variety of different automation tools are also available, so you can focus on your own websites and not on infrastructure maintenance.
[btnsx id=”2931″]
Useful links:
Customers
Twitter FEED
Recent activity
-
SecureOnlineDesktop
Estimated reading time: 6 minutes L'impatto crescente delle minacce informatiche, su sistemi operativi privati op… https://t.co/FimxTS4o9G
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The growing impact of cyber threats, on private or corporate operating systems… https://t.co/y6G6RYA9n1
-
SecureOnlineDesktop
Tempo di lettura stimato: 6 minuti Today we are talking about the CTI update of our services. Data security is… https://t.co/YAZkn7iFqa
-
SecureOnlineDesktop
Estimated reading time: 6 minutes Il tema della sicurezza delle informazioni è di grande attualità in questo peri… https://t.co/tfve5Kzr09
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The issue of information security is very topical in this historical period ch… https://t.co/TP8gvdRcrF
Newsletter
{subscription_form_1}© 2023 Secure Online Desktop s.r.l. All Rights Reserved. Registered Office: via dell'Annunciata 27 – 20121 Milan (MI), Operational Office: via statuto 3 - 42121 Reggio Emilia (RE) – PEC [email protected] Tax code and VAT number 07485920966 – R.E.A. MI-1962358 Privacy Policy - ISO Certifications