Giacomo Lanzi
Giacomo Lanzi
Manage WordPress from the hosting panel
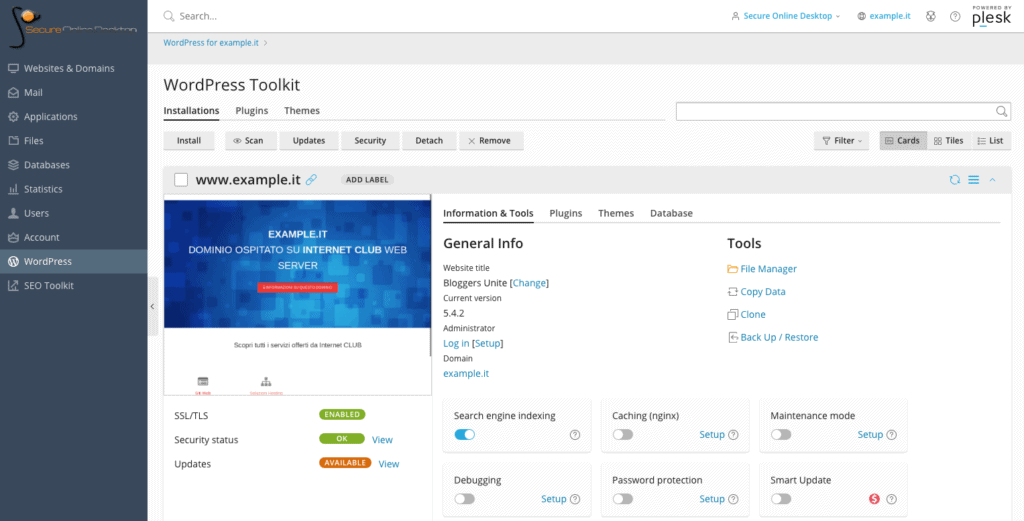
With Secure Online Desktop hosting plans, you have access to a convenient control panel. In addition to the collection of all information on the status of the server, the management of mailboxes and files, it is also possible to access a dedicated panel to manage WordPress in all its aspects. The section of the panel is called WordPress Toolkit and today we deepen it to understand when it is useful.
Manage WordPress from the hosting panel
WordPress is really widespread, so much so that 37% of all websites use this CMS. If we compare the numbers that concern only its competitors, such as Joomla !, Drupal or Wix (to name a few), then WordPress appears in 62% of web platforms that use a Content Management System. (Data from W3Techs.com)
WordPress is powerful, expandable, modular and flexible. It lends itself perfectly to build blogs, ecommerce, company sites and even forums, with the appropriate plugins. For its wide diffusion, the hosting control panel offers a special section to manage WordPress.
Install and manage a WordPress site
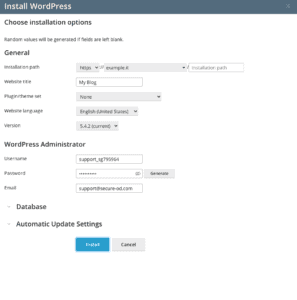
Once you have accessed the control panel, just go to the WordPress toolkit section and click on the install button. A screen will appear asking for more information for the installation.
The installation options include: installation path (different instances of WordPress can be installed on different paths), site name, theme to be installed (or plug-in packages), the language of the site and even the version of WordPress. Other options concern the administrator username and password, the database and automatic updates.
Really interesting is the possibility of installing package sets during WordPress installation. The choice includes three sets of plugins: essential, e-commerce and classic, with and without the addition of the Jetpack plugin.
Updates
Once installed, the management of the WordPress site is facilitated by being able to install, enable and disable plugins and themes on the site. Being able to do this without accessing the site backend helps to manage all the portal functions even more immediately.
It is in fact possible to update everything with a simple click, simply by pressing the updates button and then giving confirmation.
Security management
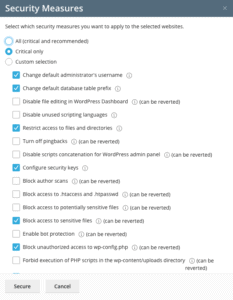 Once the site is installed, by clicking on security, you access a list of site security options. Security measures such as changing the default name of the administrator user and the prefix of the database tables are automatically recommended and enabled, but it is possible to operate options such as protecting files from the WordPress dashboard, excluding pingback and protection from bot.
Once the site is installed, by clicking on security, you access a list of site security options. Security measures such as changing the default name of the administrator user and the prefix of the database tables are automatically recommended and enabled, but it is possible to operate options such as protecting files from the WordPress dashboard, excluding pingback and protection from bot.
Everything is easily selectable from a list of items and then, by clicking on Secure, the measures are put into practice.
SEO WordPress from the hosting panel
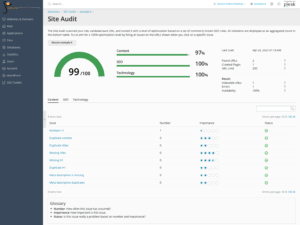
Installing, managing and securing our WordPress site are just some of the advantages that the SOD hosting control panel offers. A really interesting feature is that offered by the SEO toolkit panel.
By accessing this section of the hosting service dashboard, you access the valuable SEO information relating to the domain we are managing. It is possible to check which keywords are used on the site and the positioning of the domain in the search results.
By clicking on details, in the site audit section, you can view in detail the various factors that make up the SEO score of the site.
Importance of SEO
Most of the common SEO techniques are geared towards obtaining well-organized web pages full of interesting content for users who visit the pages. Research carried out in April 2020 shows how some of the most popular techniques have an effective impact on positioning.
Positioning in search results depends on many factors. Some depend on the quantity and density of the keywords in a text, the correctness of the content, the number of outgoing and incoming links, how the titles and other factors of this kind are written.
SEO and WordPress from the SOD hosting panel
The SOD hosting control panel provides SEO analysis and tips for the installed site. The SEO techniques to be applied to have a good positioning are deduced by analyzing the search results and checking the Google release notes regarding its indexing algorithm. SEO is therefore very important, but at the same time linked to many factors and details of a certain page or article, as we have seen before.
In the Site Audit section, under SEO toolkit, in the hosting management panel, you can find a list of possible problems and their relevance for the SEO of the domain.
The possible problems are divided into three areas: content, SEO and technology. Each entry provides a number of instances of detecting the problem on the site. By clicking on the item, information is provided on what to do and not to do regarding the topic, as well as the pages on which it was found, to correct it.
Being able to rely on a tool that analyzes and verifies SEO on your site is not at all obvious. Most of the time it would be necessary to rely on special plugins for the analysis of your site, but thanks to the functionality offered by our hosting control panel, the analysis is already available.
Conclusion
To manage a wordpress site you need patience and a good knowledge of the product. Thanks to the functionality of the SOD hosting panel, it is possible to simplify the process by centralizing the management of plugins and themes, as well as the analysis and verification of SEO techniques, in a single and convenient control panel.
You can try these features by accessing a panel demo. You can test firsthand how simple it is to have everything under control and manage your WordPress site more efficiently.
[btnsx id=”2931″]
Useful links:
CloudFlare free Plesk Webhosting users
Let’s Encrypt free certificates for all Webhosting users
Customers
Twitter FEED
Recent activity
-
SecureOnlineDesktop
Estimated reading time: 6 minutes L'impatto crescente delle minacce informatiche, su sistemi operativi privati op… https://t.co/FimxTS4o9G
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The growing impact of cyber threats, on private or corporate operating systems… https://t.co/y6G6RYA9n1
-
SecureOnlineDesktop
Tempo di lettura stimato: 6 minuti Today we are talking about the CTI update of our services. Data security is… https://t.co/YAZkn7iFqa
-
SecureOnlineDesktop
Estimated reading time: 6 minutes Il tema della sicurezza delle informazioni è di grande attualità in questo peri… https://t.co/tfve5Kzr09
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The issue of information security is very topical in this historical period ch… https://t.co/TP8gvdRcrF
Newsletter
{subscription_form_1}© 2023 Secure Online Desktop s.r.l. All Rights Reserved. Registered Office: via dell'Annunciata 27 – 20121 Milan (MI), Operational Office: via statuto 3 - 42121 Reggio Emilia (RE) – PEC [email protected] Tax code and VAT number 07485920966 – R.E.A. MI-1962358 Privacy Policy - ISO Certifications