Giacomo Lanzi
Giacomo Lanzi
Monitoring system, an overview
Estimated reading time: 5 minutes
Zabbix is a monitoring system suitable for different IT components, including networks, servers, virtual machines (VMs) and cloud services. Zabbix provides metrics such as network usage, CPU load, and disk space consumption. The software monitors operations on Linux, Hewlett Packard Unix (HP-UX), Mac OS X, Solaris, and other operating systems (OS);however, Windows monitoring is only possible through specific agents.
SOD offers you the service based on your needs. Once a first contact has been established, the customer is followed throughout the process of defining the perimeter and applying the monitoring system. Alert and control level are defined in accordance with the needs.
Monitoring system with and without agents
Zabbix can be used both with agents and without agents (software dedicated to collecting information in a system). Agents are optionally installed on IT components to monitor performance and collect data. The agent then responds to a centralized management server. This information is included in the reports or presented visually in the web-based graphical interface. If there is a problem with what is being monitored, the system sends a notification or warning to the user. Agentless monitoring performs the same type of monitoring by using existing resources in a system or device to emulate an agent.
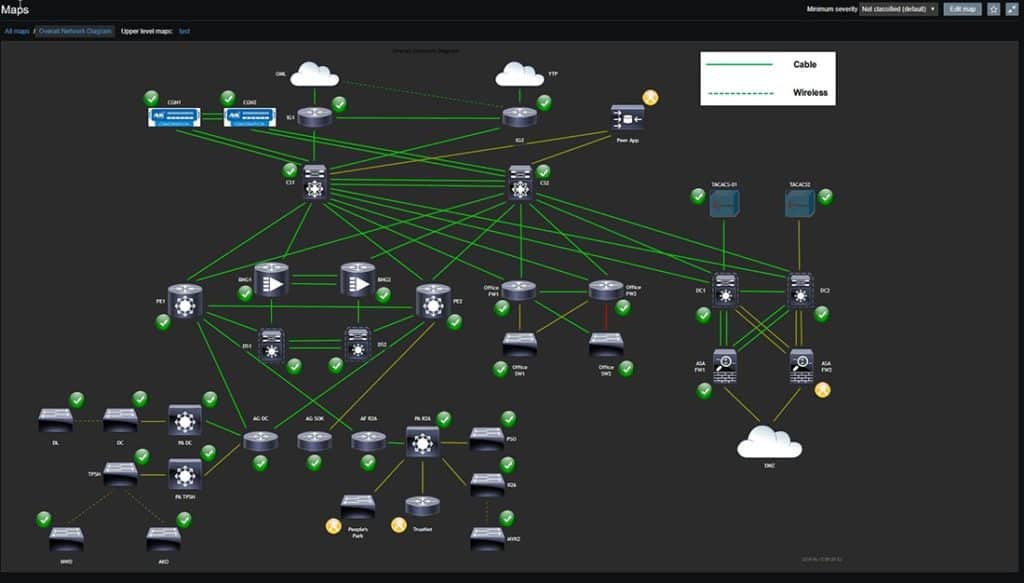
The Zabbix web-based graphical interface allows users to visualize their IT environment via customizable dashboards based on widgets, charts, network maps, slideshows and reports. For example, a user can customize a report to show metrics associated with both SLAs (Service Level Agreements) and KPIs (Key Performance Indicators) on CPU loads.
The three discovery modes
The monitoring system offered works through three discovery mode options:
– Network discovery periodically scans an IT environment and records device type, IP address, status, uptime and downtime.
– Low-level discovery (LLD) automatically creates elements, triggers and graphs based on the discovered device. Low-level discovery can create metrics from Simple Network Management Protocol (SNMP) object identifiers, Windows services, Structured Query Language (SQL) queries, network interfaces, and more.
– Auto-discovery automatically starts monitoring any device discovered using a Zabbix agent.
With the distributed monitoring system, scripts run remotely collect data from multiple devices in distributed locations and combine them into a single dashboard or report, such as server availability across the country.
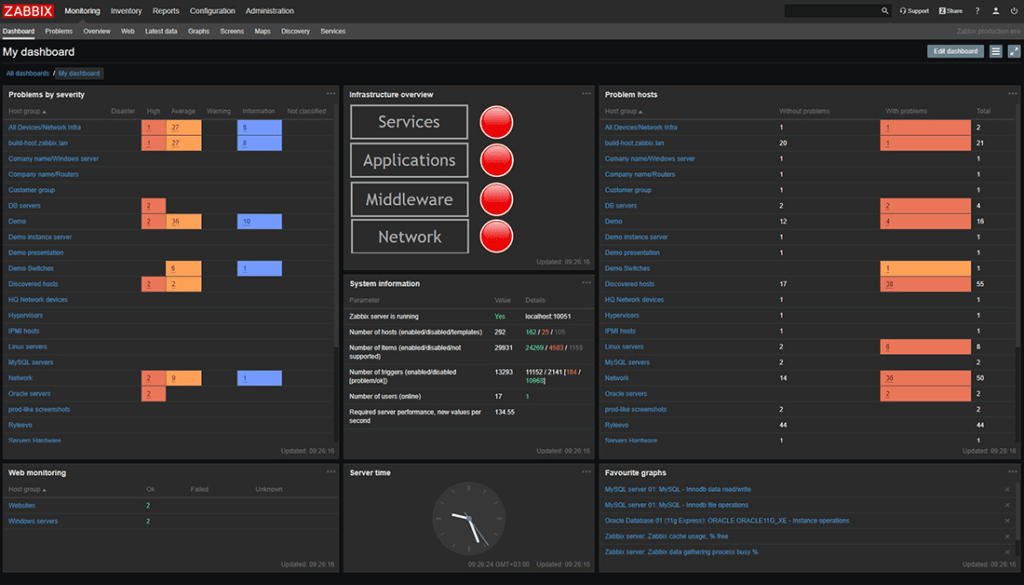
The graphical interface offers data ranging from system health to error severity and location, as well as monitoring details
The system can send notifications via e-mail, sms, telephone calls, notifications via API based on predefined events in a user’s IT environment. Another way for users to stay updated on their IT environment is through vendor applications such as M7 Monitoring or applications of their own creation.
Agentless monitoring system
Zabbix offers several monitoring options in addition to agents. A simple check can verify the availability and responsiveness of a standard service, such as notifications.
Java management extensions (JMX), web monitoring, and other methods are also alternatives to using agents. In the service offered, JMX can be used to monitor Java based applications. Web monitoring is used to check the availability of websites and supports HTTP and HTTPS. The system collects data relating to the average download speed of a scenario, errors and error messages, response times and more.
The Zabbix API
The system provides web-based APIs to create new applications, automate tasks and integrate with third-party software.The JavaScript Object Notation (JSON) format is used to use the API as a front-end web interface.
The Zabbix API consists of many methods which are grouped into separate APIs, each of which performs a specific service. For example, one method to create a new host is host.create; the method to log in as administrator is user.login. Using the API, monitoring system users can create applications to work with and view desired information.
Template
Templates are custom add-ons that extend the functionality of the monitoring system offered. Some models are made by Zabbix and come packaged with ready-to-use software, while others are built by users. Templates allow Zabbix users to monitor network devices from vendors such as Cisco, Dell, HP and Juniper. Other models can be used to monitor IBM, HP and Super Micro servers. Templates for application-based services include Microsoft Exchange and Exchange Server, Zenoss, PowerDNS, Authoritative Server Stats, and more. Templates can be created to monitor operating systems as well.
Conclusions
SOD provides an advanced monitoring system service that will allow you to keep your entire IT infrastructure under control. The monitoring possibilities are very wide and we have covered them in another article. The web interface facilitates the management and control for your perimeter, adding the possibility to set customized alarms and specific templates for every need.
If you are interested in the service, you can test it and see it working in our demo. Registration is required but no payment. Contact us for further questions or request a consultation, we are at your disposal.
Useful links:
SIEM software: what it is and how it works
ICT Monitoring Service
Acronis Active Protection: defense against ransomware
Contact us
Customers
Twitter FEED
Recent activity
-
SecureOnlineDesktop
Estimated reading time: 6 minutes L'impatto crescente delle minacce informatiche, su sistemi operativi privati op… https://t.co/FimxTS4o9G
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The growing impact of cyber threats, on private or corporate operating systems… https://t.co/y6G6RYA9n1
-
SecureOnlineDesktop
Tempo di lettura stimato: 6 minuti Today we are talking about the CTI update of our services. Data security is… https://t.co/YAZkn7iFqa
-
SecureOnlineDesktop
Estimated reading time: 6 minutes Il tema della sicurezza delle informazioni è di grande attualità in questo peri… https://t.co/tfve5Kzr09
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The issue of information security is very topical in this historical period ch… https://t.co/TP8gvdRcrF
Newsletter
{subscription_form_1}© 2023 Secure Online Desktop s.r.l. All Rights Reserved. Registered Office: via dell'Annunciata 27 – 20121 Milan (MI), Operational Office: via statuto 3 - 42121 Reggio Emilia (RE) – PEC [email protected] Tax code and VAT number 07485920966 – R.E.A. MI-1962358 Privacy Policy - ISO Certifications