Tempo di lettura stimato: 5 minutes
In un altro articolo abbiamo già parlato della Cyber Threat Intelligence spiegando cos’è, come funziona e le sue varie tipologie. Oggi, invece, ci focalizzeremo più sull’importanza della Cyber Threat Intelligence, approfondendo come può essere utile alle aziende per fornire risposte in ambito di sicurezza, contenendo i rischi e fornendo informazioni che supportino la risposta agli incidenti.
L’importanza della Cyber Threat Intelligence
In un mondo in cui le tecnologie e le minacce informatiche sono sempre in continua evoluzione, un’azienda non può permettersi di trascurare l’importanza della Cyber Threat Intelligence. Ogni giorno sul web avvengono innumerevoli attacchi informatici e furti di dati a danno di aziende e privati. Queste grandi quantità di informazioni, vengono poi catalogate e vendute illegalmente sul Dark Web.
Gli hacker sono soliti vendere informazioni in questa parte del web perché garantisce loro l’anonimato. Infatti, a differenza del web tradizionale, per poter accedere a questi luoghi virtuali, bisogna utilizzare un browser che mascheri il proprio indirizzo IP. Questo complica le attività di tracciamento dei criminali da parte delle autorità e rende il dark web un posto completamente anonimo.
Uno degli obbiettivi che si pone la CTI è quello di monitorare le informazioni presenti in questa grande parte del web a scopo analitico. Il fine è quello di prevenire e arginare i danni che questi dati potrebbero provocare.
Monitorare il Dark Web e il Deep Web
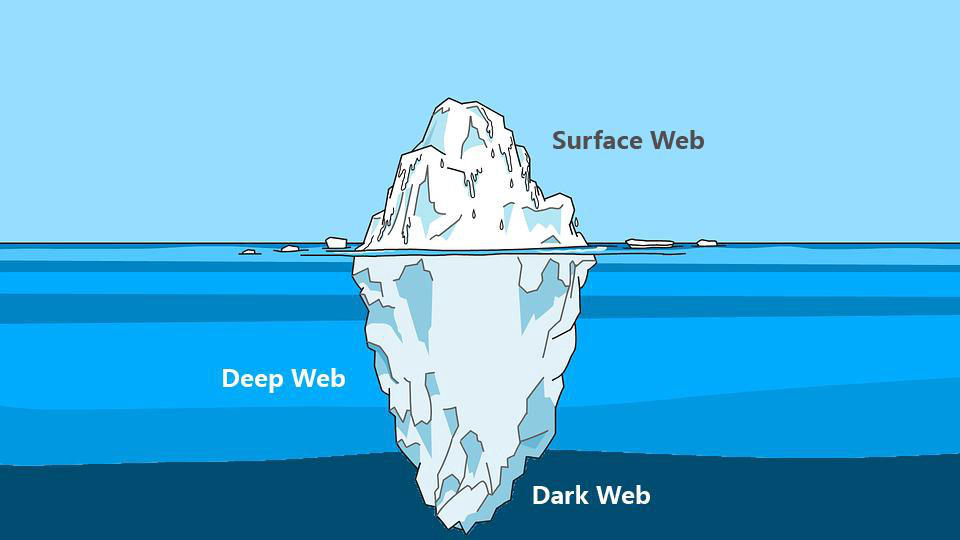
Spesso, quando parliamo di Deep Web e di Dark Web, pensiamo che siano presenti solo ed esclusivamente attività illegali, ma non è corretto. Ci sono anche forum, blog e siti web che hanno il fine di divulgare informazioni difficilmente reperibili sul web tradizionale.
Purtroppo però, è anche vero che i criminali sfruttano questa sezione della rete per vendere ogni genere di informazione. Queste comprendono numeri di telefono, indirizzi email, dati bancari, documenti, passaporti, credenziali d’accesso amministrative di siti web. C’è praticamente di tutto.
Questo genere di informazioni, nelle mani di un malintenzionato (o di un competitor), potrebbe compromettere l’integrità di un’intera azienda, dei suoi dipendenti e dei suoi clienti. Le conseguenze provocate da una violazione di dati, potrebbero inoltre manifestarsi anche sotto forma di danni alla reputazione dell’azienda.
Quando un cliente fornisce ad un’azienda i suoi dati personali si aspetta che vengano trattati con il massimo rispetto. I clienti potrebbero sentirsi “traditi” dall’azienda che avrebbe dovuto garantire loro la sicurezza delle proprie informazioni personali.
Un esempio clamoroso è stato il furto di dati avvenuto nel 2019 ai danni di Facebook Inc. (Fonte)
Ben 533 milioni di dati personali appartenenti agli utilizzatori della piattaforma sono stati sottratti, suddivisi per 106 paesi e diffusi gratuitamente sul web portando nuovamente la società al centro di polemiche.

Le aziende che cercano di proteggere i dati dei propri clienti, fornitori e dipendenti investono in strumenti di analisi e monitoraggio.
Affidandosi a dei professionisti, è possibile ricevere tempestivamente un avviso ogni qualvolta che un’informazione sensibile viene pubblicata su un forum o su un sito web presente nel Dark Web. Per questo l’importanza della Cyber Threat Intelligence gioca un ruolo chiave nel ramo della sicurezza informatica aziendale.
Monitorare il Dark Web dunque, significa avere la possibilità di poter rilevare tempestivamente eventuali informazioni sensibili prima che esse possano causare problemi alle aziende.

Strumenti per monitorare il Dark Web
Essendo una porzione di internet difficilmente accessibile e non indicizzata dai motori di ricerca, analizzare e monitorare le risorse presenti sul Deep Web diventa più complicato. Per questo motivo ci vengono in aiuto diversi strumenti progettati con lo scopo di semplificare il processo di indagine e analisi.
Un software che potrebbe essere d’aiuto durante un’attività d’investigazione è Onionscan, un programma Open Source completamente gratuito.
Il progetto Onionscan e la CTI
Il progetto Onionscan si pone due obiettivi:
– Aiutare gli operatori a trovare e risolvere problemi di sicurezza operativa
– Aiutare i ricercatori a monitorare e tracciare i siti presenti nel Deep Web
Il software è scaricabile sulla pagina Github dedicata, contenente anche una guida per l’installazione e una lista delle dipendenze necessarie per eseguire il software.
Una volta installato, per poterlo utilizzare basta semplicemente digitare nella riga di comando:
onionscan nomesitowebdascansionare.onion
Certamente, il solo accesso a uno strumento come questo non basta a fornire una copertura efficace. Infatti, l’importanza della Cyber Threat Intelligence risiede in gran parte nel saper effettuare le ricerche e interpretare i dati.
Conclusioni
Abbiamo visto cos’è e come funziona un’attività di monitoring del Dark Web e soprattutto abbiamo iniziato a comprendere l’importanza della Cyber Threat Intelligence.
Investire in queste soluzioni garantisce un’ulteriore sicurezza all’azienda. Mettere al sicuro i dati dei propri clienti e dei propri dipendenti non può essere un optional, ogni azienda dovrebbe essere sensibile a queste tematiche ed investire le proprie risorse per prevenire spiacevoli situazioni.
SOD offre un servizio apposito che si prefigge proprio di fornire informazioni di CTI preziose per la difesa proattiva e la risoluzione di criticità prima che diventino dei veri problemi.
Se hai bisogno di ulteriori chiarimenti non esitare a contattarci, siamo pronti a rispondere ad ogni tua domanda.
Useful links:
Customers
Twitter FEED
Recent activity
-
SecureOnlineDesktop
Estimated reading time: 6 minutes L'impatto crescente delle minacce informatiche, su sistemi operativi privati op… https://t.co/FimxTS4o9G
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The growing impact of cyber threats, on private or corporate operating systems… https://t.co/y6G6RYA9n1
-
SecureOnlineDesktop
Tempo di lettura stimato: 6 minuti Today we are talking about the CTI update of our services. Data security is… https://t.co/YAZkn7iFqa
-
SecureOnlineDesktop
Estimated reading time: 6 minutes Il tema della sicurezza delle informazioni è di grande attualità in questo peri… https://t.co/tfve5Kzr09
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The issue of information security is very topical in this historical period ch… https://t.co/TP8gvdRcrF
Newsletter
{subscription_form_1}© 2024 Cyberfero s.r.l. All Rights Reserved. Registered Office: via statuto 3 – 42121 Milan (MI) – PEC [email protected] Tax code and VAT number 07485920966 – R.E.A. MI-1962358 Privacy Policy - ISO Certifications












