
Estimated reading time: 5 minutes
Just like any other IT field, the cybersecurity market is driven by hype . Currently hype towards XDR, ie eXtended Detection and Response .
XDR is the latest in threat detection and response, a key element of a company’s infrastructure and data defense .
What exactly is XDR?
XDR is an alternative to traditional responsive approaches that only provide layer visibility on attacks . I refer to procedures such as detection and endpoint response (EDR), network traffic analysis (NTA) and SIEM , which we have talked about in many other articles.
The layer visibility implies that various services are adopted, stratified (layers), which each keep under control a specific entity in the infrastructure. This can be problematic. In fact, you need to make sure that layers don’t end up isolated, making it difficult, or nearly impossible to manage and view data. layer visibility provides important information, but can also lead to problems, including :
Collecting too many incomplete and contextless alerts. EDR detects only 26% of initial attack vectors and due to the high volume of security alerts, 54% of professionals security ignores warnings that should be investigated .
Complex and time-consuming investigations requiring specialist expertise . With EDR, the median time to identify a breach has increased to 197 days, and the median time to contain a breach has increased to 69 days.
Tools focused on technology rather than user or business . EDR focuses on technology gaps rather than the operational needs of users and companies. With more than 40 tools used in an average Security Operations Center (SOC), 23% of security teams spend their time maintaining and managing security tools rather than investigating . ( Source )
For already overloaded security teams, the result can be an endless stream of events , too many tools and information to switch between, longer time frames for detection and security expenses that are beyond budget and are not even fully effective .
What’s new in eXtended Detection Response
XDR implements a proactive approach to threat detection and response . It offers visibility into data across networks, clouds and endpoints, while applying analytics and automation to address today’s increasingly sophisticated threats. The benefits of the XDR approach for security teams are manifold:
Identify hidden, stealth and sophisticated threats proactively and quickly.
Track threats across any source or location within your organization. < br> Increase the productivity of people working with technology.
Get more from their security investments .
Conclude investigations in a way more efficient .
From a business perspective, XDR enables companies to detect cyber threats and stop attacks, as well as simplify and strengthen security processes. As a result, it enables companies to better serve users and accelerate digital transformation initiatives. When users, data and applications are protected, companies can focus on strategic priorities.
Why consider it for your company
The two main reasons why this approach is beneficial are: endpoints do not have visibility into threats in places like cloud services , and it may not be possible to put a < em> software agent on all company endpoints .
But there are other reasons to consider too. The addition of other data sources can provide more context in the EDR results, improving triage and investigation of alerts . Providers are moving not only to provide more and better organized data, but also by delivering analytics platforms to lighten the analytical load on operators. This translates into ease of use and reduced operating costs.
XDR can seem very attractive as a product: Tight integration of parts, highly tuned content (as the provider has total control over the events from the data sources), use of analytics and response automation.

What to pay attention to before adoption
Some providers are positioning their XDR as the ultimate threat detection solution . However, many vendors are unable to offer all the tools needed to get the advantage sold. Some providers offer endpoint and cloud monitoring in the package, others endpoint and network monitoring, but when looking at the comprehensive needs of most organizations, there are often missing details in the overall picture.
And if, once the company engages with a provider and notices a lack in one of the monitored sectors, what are the possible solutions? A situation of vendor lock-in from which to break free means to sever a contract and then open another one, with all the consequent costs.
XDR as an approach, not as a product
Before entering into a contract with a provider that sells a solution as final, it is always good to weigh the benefits and implications analytically.
Tight, two-way integration of multiple threat detection and response capabilities is the first distinguishing feature. But it is not necessary to buy two technology components from the same vendor to achieve good integration. Indeed, many products have the ability to integrate with some solutions from other vendors as one of their main strengths.
The XDR approach must provide a platform that allows the necessary data collection and storage , but also strong analytical skills, to orchestrate and automate response actions provided by the other parts of the solution. A cloud based Next Generation SIEM is a perfect solution.
How to move then?
The interest in XDR products is a clear signal that excessive fragmentation was leading to excessive complexity. A little consolidation is good, but it must be done while protecting flexibility and the ability to follow the best solutions.
In our opinion, a SOCaaS is an optimal solution. Provides next generation SIEM , with strong analytical capabilities. In addition, it also integrates artificial intelligence that helps in time to recognize threats through behavior analysis. A SOCaaS is the future of security operating platforms.
To find out with our services they can help you protect the data of your company and your customers, contact us, we will gladly answer all your questions.
Useful links:

Estimated reading time: 6 minutes
I dati di threat intelligence forniscono alle aziende approfondimenti rilevanti e tempestivi necessari per comprendere, prevedere, rilevare e rispondere alle minacce alla sicurezza informatica. Le soluzioni di intelligence sulle minacce raccolgono, filtrano e analizzano grandi volumi di dati grezzi relativi a fonti esistenti o emergenti di minacce. Il risultato sono feed di threat intelligence e rapporti di gestione. I data scientist e i team di sicurezza utilizzano questi feed e report per sviluppare un programma con risposte mirate agli incidenti per attacchi specifici.
Tutti, dalla prevenzione delle frodi alle operazioni di sicurezza all’analisi dei rischi, traggono vantaggio dalla threat intelligence. Il software di intelligence sulle minacce fornisce visualizzazioni interattive e in tempo reale dei dati relativi alle minacce e alle vulnerabilità.
Il vantaggio offerto agli analisti ed esperti di sicurezza è evidente e serve a identificare facilmente e rapidamente i modelli degli attori delle minacce. Comprendere la fonte e l’obiettivo degli attacchi aiuta i capi d’azienda a mettere in atto difese efficaci per mitigare i rischi e proteggersi dalle attività che potrebbero avere un impatto negativo sull’azienda.
La cyber threat intelligence può essere classificata come strategica, tattica oppure operativa. Quella Strategica riguarda le capacità e gli intenti generali degli attacchi informatici. Di conseguenza anche lo sviluppo di strategie informate associate alla lotta contro le minacce a lungo termine. Quella Tattica riguarda le tecniche e le procedure che gli aggressori potrebbero utilizzare nelle operazioni quotidiane. Infine, la threat intelligence Operativa, fornisce informazioni altamente tecniche a livello forense riguardanti una specifica campagna di attacco.

Il ciclo della threat intelligence
Le soluzioni di intelligence sulle minacce raccolgono dati grezzi sugli attori e le minacce da varie fonti. Questi dati vengono poi analizzati e filtrati per produrre feed e rapporti di gestione che contengono informazioni che possono essere utilizzate in soluzioni automatizzate di controllo della sicurezza. Lo scopo principale di questo tipo di sicurezza è quello di mantenere le organizzazioni informate sui rischi delle minacce persistenti avanzate, delle minacce zero-day e degli exploit, e su come proteggersi da esse.
Il ciclo di intelligence delle minacce informatiche consiste nelle seguenti fasi.
Pianificazione: I requisiti dei dati devono essere prima definiti.
Raccolta: Si raccolgono grandi quantità di dati grezzi da fonti interne ed esterne di threat intelligence.
Elaborazione: I dati grezzi sono filtrati, categorizzati e organizzati.
Analisi: Questo processo trasforma i dati grezzi in flussi di informazioni sulle minacce con l’uso di tecniche analitiche strutturate in tempo reale e aiuta gli analisti a individuare gli indicatori di compromissione (IOC).
Diffusione: I risultati dell’analisi vengono immediatamente condivisi con i professionisti della sicurezza informatica e gli analisti di threat intelligence.
Feedback: Se tutte le domande trovano risposta, il ciclo si conclude. Se ci sono nuovi requisiti, il ciclo ricomincia dalla fase di pianificazione.
Indicatori comuni di compromissione
Le aziende sono sempre più sotto pressione per gestire le vulnerabilità della sicurezza e il panorama delle minacce è in continua evoluzione. I feed di threat intelligence possono aiutare in questo processo identificando gli indicatori comuni di compromissione (IOC). Non solo, possono anche raccomandare i passi necessari per prevenire attacchi e infezioni. Alcuni degli indicatori di compromissione più comuni includono:
Indirizzi IP, URL e nomi di dominio: Un esempio potrebbe essere un malware che prende di mira un host interno che sta comunicando con un noto attore di minacce.
Indirizzi e-mail, oggetto delle e-mail, link e allegati: Un esempio potrebbe essere un tentativo di phishing che si basa su un utente ignaro che clicca su un link o un allegato e avvia un comando dannoso.
Chiavi di registro, nomi di file e hash di file e DLL: Un esempio potrebbe essere un attacco da un host esterno che è già stato segnalato per un comportamento nefasto o che è già infetto.

Quali strumenti per la threat intelligence
Il crescente aumento del malware e delle minacce informatiche ha portato a un’abbondanza di strumenti di threat intelligence che forniscono preziose informazioni per proteggere le aziende.
Questi strumenti si presentano sotto forma di piattaforme sia open source che proprietarie. Queste forniscono una serie di capacità di difesa contro le minacce informatiche, come l’analisi automatizzata dei rischi, la raccolta di dati privati, strumenti di ricerca rapida di threat intelligence, la segnalazione e condivisione di queste informazioni tra più utenti, avvisi curati, analisi dei rischi di vulnerabilità, monitoraggio del dark web, mitigazione automatizzata dei rischi, threat hunting e molto altro.
Abbiamo parlato di uno di questi strumenti in un altro articolo: il Mitre Att&ck. Questo è uno strumento molto utile per conoscere i comportamenti e le tecniche di attacco hacker. Questo grazie alle informazioni raccolte dalla threat intelligence e la conseguente condivisione. Un framework come questo è molto efficiente per creare meccanismi difensivi che consentono di mettere in sicurezza le infrastrutture aziendali.
Intelligenza artificiale e informazioni sulle minacce
Come abbiamo visto prima, la raccolta di informazioni da varie fonti non è altro che una delle fasi. Queste devono poi venire analizzate e successivamente elaborate in protocolli di controllo, per essere davvero utili per la sicurezza.
Per questo tipo di lavori di analisi, definizione di comportamenti baseline e controllo dei dati ci si affida sempre di più all’intelligenza artificiale e al deep learning. Un Next Generation SIEM, affiancato a una soluzione UEBA sono perfetti per questo tipo di protezione.
Il controllo del comportamento delle entità all’interno del perimetro effettuato dal UEBA è in grado di identificare ogni comportamento sospetto, in base alle informazioni raccolte e analizzate dal SIEM.
Conclusioni
Gli strumenti di difesa che abbiamo nominato sono il valore primario di un piano di sicurezza aziendale. Adottare soluzioni specifiche, implementare la threat intelligence e quindi una ricerca attiva degli indicatori di minacce, offre una posizione di vantaggio strategica. L’azienda può operare un passo avanti ai criminali, i quali possono far leva solo sull’effetto sorpresa contro le loro vittime. Proprio per questa situazione generale, ogni azienda dovrebbe essere nelle condizioni di non farsi cogliere alla sprovvista. Implementare soluzioni proattive è ormai necessario.
La threat intelligence è quindi un’arma da difesa dietro la quale mettere al riparo le risorse più importanti per poter lavorare in tranquillità.
Se vuoi sapere come possiamo aiutarti con i nostri servizi dedicati alla sicurezza, non esitare a contattarci, saremo lieti di rispondere a ogni domanda.
Useful links:
Cyber Threat Intelligence (CTI) – maggiore efficacia per la sicurezza IT
Progetti di Secure Online Desktop
Cos’è la Cyber Security? Definizione e proposte
Prevenire il shoulder surfing e il furto di credenziali aziendali

Estimated reading time: 4 minutes
When we refer to artificial intelligence, we often refer to the great technologies that could control the world, with an obvious streak of science fiction. The reality is very different and is characterized by a technology with great potential, which is able to ensure countless advantages . Today we talk about how artificial intelligence can be implemented in monitoring.
The use of these technologies is unavoidably transversal to many sectors of the economy, but it is also usable in some aspects of everyday life. Some examples range from washing machines that, weighing the load of laundry, are able to choose the most advantageous washing program, to voice assistants that simplify our everyday life.
Very important in the corporate sector are the monitoring systems which were created precisely from these technologies which we will talk more about in a moment.
Thanks to the optimization of the computing capacity operated by artificial intelligence, it is possible to increase the efficiency of company equipment. Let’s see how.

What is artificial intelligence and how can it innovate monitoring ?
Today, artificial intelligence is declined in many ways. Perhaps the most important is processing a large amount of data then providing answers to complex questions. At the base of artificial intelligence there is the study of algorithms that deal with performing complex mathematical operations.
Artificial intelligence is a very useful tool within a company, as it is able to carry out very sophisticated and precise processing. These operations are capable of significantly improving the operations and productivity of numerous departments of the company itself.
Applied to monitoring, for example, artificial intelligence is capable of analyzing the logs coming from the network, both in terms of performance and behavior. The big step forward in the analysis and monitoring of an infrastructure consists precisely in recognizing whether certain behaviors that emerge from the logs are risky or not.
To achieve these results it is essential to have all those features that are available through artificial intelligence .
What are the advantages of using artificial intelligence for monitoring?
Artificial intelligence is able to provide companies that choose to use it countless advantages. Not only in terms of improving the performance of information systems, but also to make more efficient and improve the security of the same, preventing attacks.
This happens thanks to the analysis of the logs both from a technical and a behavioral point of view. Technical analysis highlights any ongoing problems, while behavioral analysis can prevent or immediately identify suspicious actions.
How can our monitoring system improve business efficiency?
Our monitoring system is able to improve business efficiency through numerous technical analyzes in able to be implemented not only on the entire system, but also on individual units.
The ability to analyze data in depth also allows you to improve the management of the entire IT structure and prevent overloads or attacks. Overall, the efficiency and safety of the infrastructure are increased at the same time through artificial intelligence applied to monitoring.
But there’s more: these analysis and monitoring systems are able to integrate with extreme effectiveness in complex architectures. By being able to analyze large amounts of data and being able to deduce behaviors and actions from these, efficiency in security is ensured.
Another advantage is the fact that this monitoring system does not require specific hardware. Software agents are installed on the systems to be controlled which have the sole task of sending data in the form of a log to the control system. analyses.
These systems therefore prove to be the ideal solution to keep large and small IT architectures under control, with the aim of improving efficiency and increasing overall security. In short, an application really interesting and useful of artificial intelligence in monitoring.

What are the fields of application of this technology?
We apply artificial intelligence systems to monitoring, benefiting our customers enormously. First we can collect large amounts of data, enrich it automatically and finally analyze it. The analyzes are carried out both from a technical and a behavioral point of view.
The result is a dedicated system, our SOCaaS, which makes risk mitigation extremely efficient, particularly quick intervention in the event of an anomaly and also provides regular reports.
This service is able to bring together all the features listed in the article, and to offer it as a solution for companies that want a superior security system.
Better efficiency, safety, versatility, operability, are just some of the paradigms used to define the services we make available to our customers. Our main goal is to simplify and make your company’s IT security more efficient.
Do not hesitate to contact us if you want to know more, we will be happy to answer any questions.
Useful links:

Estimated reading time: 7 minutes
When we talk about log management we refer to a precise process which consists of the centralized collection of data that comes from different operating environments such as: devices, databases, applications and much more. Logs are produced by various system events , many of which are particularly important in the business environment.
So let’s see some important details regarding log management.

The importance of collection-in-log-management
The procedure for collecting log data is important to achieve various objectives at the company level. The main ones are: to verify the vulnerability; manage possible security problems; control access to data and applications; the monitoring in real time ; check for any malfunctions at the application level.
From a regulatory point of view, then, log management is very important at a company level as allows you to observe the most important principles concerning data protection . This is established by the “EU 95/46 / EC” directive. It is also required by the obligations established by the “ General Data Protection Regulation (RGPD or GDPR) “.
Hence, these features illustrate how important good log management is and how it can help companies prevent potentially invasive events before they occur.
This type of action corresponds to what, in jargon, is called “Privacy by Design”. According to this principle, it becomes necessary to execute the right strategies to avoid creating risks and problems related to violations.
The-problems-to-face-in-log-management
Log management needs the correct balance between the dynamic availability of resources and the growing number of log data . In addition, from the first step of acquiring the log data, it is appropriate to consider several elements. These often generate various complexities such as, for example: the quantity of sources to be taken into account; the number of data logs created; the multiplicity of events that give life to data log ; the types of data log ; the method of acquiring the data logs ; the compliance of the data log protection systems.
Log management needs the correct balance between the dynamic availability of resources and the growing number of log data . In addition, from the first step of acquiring the log data, it is appropriate to consider several elements. These often generate various complexities such as, for example: the quantity of sources to be taken into account; the number of data logs created; the multiplicity of events that give life to data log ; the types of data log ; the method of acquiring the data logs ; the compliance of the data log protection systems.
It is therefore advisable to plan the strategies that allow you to adopt the right solutions for your log management staff. In this way, technicians will be able to intervene while respecting the requirements already mentioned.
The characteristics of a log-management infrastructure
The infrastructure for log management is formed by the union of hardware, software and network elements that are set up so that they can communicate effectively with each other. The communications between these components are made within the same network that is used for the common activities of the company.
Nevertheless, for a company it is also important to take into account the possibility of collecting data using a different network so that any spyware attacks or other incidents will alter, intercept or delete the data.
If from the logistical and architectural point of view it is not possible, in a company, to carry out this second possibility, alternative measures should be adopted such as, for example, data encryption.
Summarizing, therefore, a log management infrastructure should ensure compliance with the following requirements: maintaining information that serves to achieve the collection objective following the principles of “minimization” and “proportionality” ; ensure that data remain unalterable throughout their life span; ensure the integrity of the data collected without making changes; keep the data for a limited period of time.
The data-aggregation at the company-level
As companies grow and reach large numbers of applications within their environment, data collection becomes an increasingly important and decisive challenge.
In addition, if we take into account the difficulty of collecting sufficient data logs to be able to remain compliant, respect for privacy standards and security issues that arise from modern threats, we easily realize how the collection becomes an increasingly complex challenge.
So, at the enterprise level, the key to creating an efficient collection system is the ability to dynamically capture data in real time from all available sources. Have a solution that allows you to put your data in a central location, such as a data lake , and facilitate filtering , transformation, classification, allows you to make the log management task easier for the company.
SOCaaS and the advanced log management system
A very advanced solution is the one offered by the SOCaaS , in particular by its component SIEM , which leverages the innovation of artificial intelligence. This allows you to analyze the data collected so as to find possible suspicious data.
In addition, a qualified technical intervention is always made available at any time of the day with precise and non-distracting tasks. The intervention allows you to verify the alarm notifications that are generated by the system so as to exclude false positives , intervening to eliminate the threat and give constant reports over time .
The ever increasing data collection and the analysis of artificial intelligence allow to make the service very convenient and complete.
The potential of the SOCaaS-system for companies
As we have just seen, it is very convenient for companies to rely on a SOC service (SOCaaS). The greatest potential is represented precisely by the innovation brought about by artificial intelligence that allows you to achieve maximum results regarding the constant and continuous analysis of data so that it has the certainty of identifying possible threats in a very short time . Thanks to this system, therefore, risks will be prevented and mitigated.
An added value, then, is not having to hire specialized technicians with specific skills in identifying and verifying threats. Those who rely on this service will also be able to receive reports on the situation and notifications in case of problems.
SOCaaS, therefore, allows you to take the right precautions against those still unknown techniques and has the ability to find the link between data concerning possible attacks with still unknown systems. This is thanks to the analysis of user behavior and infrastructure intities ( UEBA ).
In addition, the structure of the system is designed to bring about constant improvement. The synergistic work between technicians and artificial intelligence allows us to identify even unconventional breach attempts.
For companies it means improving their defenses by adapting them based on the data collected previously.
SOCaaS is perfect for those companies that want to work safely using network-based infrastructures. This is a guarantee of defense against cyber attacks .

The-advantages of choosing our SOCaaS for log-management
Choosing to rely on our SOCaaS has several benefits.
The first is to save money in both the short and long term. In fact, you will avoid buying dedicated hardware and specific software . Plus, you won’t even need to hire new employees or upgrade the skills of those who already work.
Another benefit is having the professional support of technicians who update every day to have the skills to fight new types of threats. This type of assistance is priceless and it is extremely difficult to obtain within the company staff. This is also due to the current shortage of professionals in the sector.
A further advantage is to have always updated technology available . You will not have to worry and worry about always updating the software, because these, solely responsible for the collection of data for SOCaaS, are always kept to the latest version.
Do you want to get more information to learn more about the SOCaaS functionality of SOD? Contact us to find out how we can help you keep your company’s defenses up.
Useful links:
Estimated reading time: 6 minutes
Today we see one of the latest additions to our SOCaaS, the Autonomous Threat Sweeper (ATS) . A system able to support SOC in an innovative way and protect against the most innovative threats.
The Privacy Guarantor, through the provision dated May 27, 2021, has introduced some changes regarding the violation of sensitive and personal data. A particular reference was made to the numerous cases of data breach. In essence, the legislation relating to the notification system has been tightened . The legislation provides for the application of a certain procedure to be adopted in the event of a data breach.
It is not easy to stay up to date on the continuous regulations on privacy, nor to have IT threat prevention systems available such as i ransomware working in the shadows and increasingly aggressive and dangerous. For this reason, threat protection has become an issue that is no longer easily manageable through non-professional systems . Today specific IT skills are constantly updated and professionals working in the sector, especially for companies.

Context: the unstoppable growth of ransomware
As we know, the term ransomware defines a category of malware capable of encrypting the files and documents contained in the attacked computer, in some cases even on the network to which it is connected. We have seen this in various articles through known examples .
In recent years, ransomware has spread enormously, so much so that it is listed as the most dangerous cyber threat to businesses .
Among the main companies targeted are those that have a large amount of sensitive data which, if stolen, would expose the company to the distrust of their customers. The encryption of the files stored inside the devices is, therefore, resolved only following the payment of a ransom.
Unfortunately, once compromised, the system does not allow users to access the data on their devices, effectively preventing their use.
Currently, ransomware is one of the main cyber threats, so much so that it is categorized as a profitable business model. This is because of the constant improvements made to their software that make it easier for hackers to use. The result is an increasing number of attacks performed with tools that required almost no specific skills.
IT security: increased risk = increased insurance policies
In terms of computer security, the aspects to consider are different, among these, in fact, there is the one related to ransomware software. These require a greater definition of reporting requirements in the event of a data breach due to an increase in systemic risk.
This problem has led to an increase in the prices of the insurance market. As these threats, in addition to being more and more frequent, are the cause of high damage to companies, insurance companies have raised their prices. But not only that, today they also demand specific requirements from the policyholders, to demonstrate the use of adequate defense systems in the IT field.
Autonomous Threat Sweeper: the new technology integrated in SOCaaS
Preventive malware detection is the priority solution to be adopted in order to avoid the risk of being attacked by malware that can steal company data.
What is worrying, however, is not only the increase in the cost of insurance, but the greater definition of the required requirements. The requirements, that is, relating to the reports to be forwarded in the event of a data breach and the consequent increase in systemic risk .
The SOC as a Service is a service entirely dedicated to the IT security of companies, which involves data collection and enrichment aimed at proactive identification of social engineering attacks. The system includes a Security Data Lake (SDL), the event and information management (SIEM) and l ‘user behavior analysis (UEBA).
Through the Autonomous Threat Sweeper (ATS) the team is able to provide companies with 24/7 coverage through an automatic search. This, once activated, is able not only to to prevent attacks from the outside, but also to detect any malware previously installed on company devices.
This system allows you to automate the rapid detection of these threats. Once identified, it is easy to implement targeted actions in order to counter their attacks. Since cyber attacks are and will always be present in everyday business life, it is certainly important to be well equipped. Attacks will continue to grow in breadth and scale and let’s not forget the trend in the shortage of technicians . We can only bring into play systems that automate the first stages of control and detection.
The Autonomous Threat Sweeper (ATS) is currently one of the few systems capable of pre-coding the latest generation of cyber attacks . Its coverage includes corporate networks and devices.

Autonomous Threat Sweeper (ATS)
Autonomous Threat Sweeper (ATS) is a constantly updated system capable of detecting the latest generation threats. This guarantees companies that turn to us to always be protected from the latest generation IT risks to infrastructures and devices.
We have already talked about SIEM , software tools able to provide cyber security professionals with an analysis of logs and events to provide real-time threat minitoring. Here, the ATS even improves the functionality of software as complex and accurate as SIEM, making it capable of detecting low and slow threats through post-hoc.
Basically, with the ATS it will be possible to speed up the process of detecting threats in order to avoid damage that also compromises the strength of the infrastructure.
Conclusions: How to behave in case of violation
In the event that an IT breach occurs, with or without intent, involving the loss, destruction, modification or unauthorized disclosure or unauthorized access to the data processed by a company, the data controller appointed by the same must notify the violation within 72 hours.
Subsequently, investigations could take place to understand the extent of the damage and then also penalties in case of negligence. By adopting an Autonomous Threat Sweeper your business will be able to intercept threats before they can do any harm.
Preventing data breaches, ransom requests and other cyber security attacks is easy if you turn to competent people. Ask us for more details on how we can support your company with regards to cybersecurity. We will be happy to answer all your questions.
Useful links:
Webinar: SOCaaS (Security Operation Center as a Service) e NGS (Next Generation SIEM)
Pass the Ticket: how to mitigate it with a SOCaaS
Use cases of a SOCaaS for companies part 2
Use cases of a SOCaaS for companies part 1
Predictive cybersecurity with our SOCaaS

Cyberattacks are numerous and do not distinguish between companies and individuals when targeting a target. You’ve most likely heard the term “cyber threat” in the media before, but what exactly are we talking about? Other ways you may have heard this are “cyberthreat”, “cyberattack” or similar.

What is a Cyber Threat?
Today the term “cyber threat” is used predominantly in the world of information security.
A cyber threat is a malicious act conceived with the purpose of damaging systems, stealing data or any purpose that has the purpose of causing damage of any kind. Viruses, data breaches and DDoS attacks are included. Even if the threat is virtual, what is real is the attacker’s intent as well as the potential impact. While many cyberattacks are mere nuisances, some are quite serious. Some even potentially threaten human lives.
The potential impact that these kinds of attacks can have is often underestimated. Most of the time, the attacks are easily identifiable and do not pose much risk. Instead, other times it happens to come across some more sophisticated threats, difficult to identify, which represent a big problem even for many companies.
Cyber threats are a major concern for businesses. Cyberattacks can lead to power outages, government equipment failures, and breaches of state secrets. They can manipulate telephone and computer networks or, as in the case of ransomware, they can cripple entire systems by making data inaccessible.
Every day new companies and organizations set foot in the digital world with awareness of the risks associated with their technological infrastructures. In some cases, cyber threats are underestimated and this often means great economic and image damage for the company that has underestimated cyber threats and security.
The increase in IT-related risks is real, as are data security solutions. The best thing to do is to take the necessary safety measures right away.
Types of Cyber Threats
The types of cyber threats are numerous, and it must also be considered that they are constantly evolving. The intent of hackers is usually to secure an economic gain by carrying out sabotage, espionage or data theft operations. As a result, they can be expected to do everything possible to achieve their ends.
Virtually every cyber threat falls into one of the following ten types of risks. Hackers have an abundance of options to choose from in order to operate. Furthermore, computer literacy is all in all poor, so hackers often have an easy time, especially for small local realities.
The 10 most common types of computer threats
Malware
It is a type of software that executes a malicious command on a device or within a computer network, corrupting data or taking control of the system.
Phishing
Phishing is an e-mail attack that consists of tricking the recipient into revealing confidential information or inviting him to download malware by clicking on a link in the body of the message. These are real scams, which we have talked about extensively in other articles. Often they don’t even involve great IT skills on the part of the attacker, just a little social engineering.
Vishing
Vishing is a more sophisticated form of phishing in which the hacker uses VoIP technology to contact the victim, attempting to trick them. There is also a variant that instead uses text messages to attack, it is called smishing.
Man in the Middle
As the name suggests, this type of attack refers to when a hacker intervenes in a conversation posing as one of the two parties, with the aim of stealing sensitive information. What we often don’t think about is that the conversation is between two machines and therefore not immediate to monitor.
Trojan viruses
The origin of its name is inspired by the famous Trojan Horse of ancient Greece. Trojan is a type of malware that infiltrates a computer system by hiding its true nature. For example, it could impersonate known software and then release malicious code once inside the host device.
Ransomware
Ransomware is an attack that uses encryption to make information on a system inaccessible. The aim is to demand a ransom in exchange for being able to access the data again. Possibilità che a volte, in realtà, non è nemmeno assicurata.
DDoS attack
It occurs when the attacker uses many devices to overload a target, such as a website, with requests, causing it to crash or become instabilities.
Attacks on IoT devices
This is an increasingly popular attack due to the nature of the targets. Devices such as sensors or industrial plants connected to the network are vulnerable to multiple types of cyber threats. The hacker could take control of the device and then later use it in a DDoS attack. Alternatively it could steal the information present in the device itself obtaining important data to continue the attack. Given their number of frequently out-of-date operating systems, IoT devices are a very attractive target.
Malware in mobile applications
Phones and tablets are just as vulnerable to malware as any other device. È possibile inserire malware all’interno di app, nei siti web o nelle e-mail sfruttando il phishing. Once compromised, a mobile device can provide access to personal information, location data, and financial accounts.
A recent example of this type of eventuality is Pegasus software, which is used to monitor and collect data from journalists around the world. (Source: The Guardian)
Practical defense and prevention solutions
Cyber threats are always expanding and improving. Millions of them are created every year, many of them follow the aforementioned characteristics, but others are technologically more complex and more powerful.
Fortunately, however, there are also more and more highly qualified companies in the field of IT security that offer cutting-edge tools and services that help prevent, identify and promptly block all kinds of IT attacks.
Threat detection tools
Threat detection tools are an essential part of a company’s cybersecurity technology stack. Threat detection is also the first defense against any Cyber Threat.
Specific solutions, such as the use of a SOCaaS, for example, are of vital importance for safeguarding an IT infrastructure, thanks also to the integration of the SIEM engine which includes UBA and UEBA, guaranteeing complete control also over the users.
Another useful tool is definitely ACP. Acronis Cyber Protect is a solution that integrates data protection and management to safeguard your endpoints, data and systems. Its automation capabilities provide unparalleled protection, enabling businesses to increase their productivity and reduce risk.
Vulnerability Assessment & Penetration Test (VA-PT)
Services like VA & PT are field tests that test the infrastructure in a concrete context. Our teams of white hat hackers find vulnerabilities within the system to point the finger at weaknesses to fix.

Conclusions
We have learned what a cyber threat is and its most common types, also discovering which solutions can be adopted in order to guarantee better corporate and employee safety.
What countermeasures has your company taken to protect your safety? If you would like more information about it, you can contact us by pressing the button below. We offer ad hoc services and solutions to strengthen corporate defenses.
Useful links

Estimated reading time: 5 minutes
With the advent of big data platforms, IT security companies can now make guided decisions on how to protect their assets. By recording network traffic and network flows, it is possible to get an idea of the channels on which company information flows. To facilitate the integration of data between the various applications and to develop new analytical functionalities, we the Apache Open Data Model meets.
The common Open Data Model for networks, endpoints and users has several advantages. For example, easier integration between various security applications, but companies are also made it easier to share analytics in case new threats are detected.
Hadoop offers adequate tools to manage a Security Data Lake (SDL) and big data analysis. It can also detect events that are usually difficult to identify, such as lateral movement , data leaks, internal problems or stealth behavior in general. Thanks to the technologies behind the SDL it is possible to collect the data of the SIEM to be able to exploit them through SOCaaS since, being a free Open Data Model, the logs are stored in such a way that they can be used by anyone.

What is Hadoop Open Data Model
Apache Hadoop is free and open source software that helps companies gain insight into their network environments. The analysis of the collected data leads to the identification of potential security threats or any attacks that take place between the resources in the cloud.
While traditional Cyber Threat Intelligence tools help identify threats and attacks in general, an Open Data Model provides a tool that allow companies to detect suspicious connections using flow and packet analysis.
H adoop Open Data Model combines all security-related data (events, users, networks, etc.) into a single visual area that can be used to identify threats effectively. It is You can also use them to create new analytical models. In fact, an Open Data Model allows the sharing and reuse of threat detection models.
An Open Data Model also provides a common taxonomy to describe the security telemetry data used to detect threats. Using data structures and schemas in the Hadoop platform it is possible to collect, store and analyze security-related data.
Open Data Model Hadoop, the advantages for companies
- – Archive a copy of the data security telemetry
- – Leverage out-of-the-box analytics to detect threats targeting DNS, Flow and Proxy
- – Build custom analytics based on your needs
- – Allows third parties to interact with ‘Open Data Model
- – Share and reuse models of threat detection, algorithms, visualizations and analysis from the community Apache Spot .
- – Leverage security telemetry data to better detect threats
- – Using security logs
- – Obtain data from users , endpoints and network entities
- – Obtain threat intelligence data
Open Data Model: types of data collected
To provide a complete security picture and to effectively analyze cyber threat data, you need to collect and analyze all logs and alerts regarding security events and contextual data related to the entities you are dealing with referenced in these logs . The most common entities include the network, users and endpoints, but there are actually many more, such as files and certificates.
Due to the need to collect and analyze security alerts, logs and contextual data, the following types of data are included in the Open Data Model.
Security Event Alerts in Open Data Model
These are event logs from common data sources used to identify threats and better understand network flows. For example operating system logs, IPS logs, firewall logs, proxy logs, web and many more.
Network context data
These include network information that is accessible to anyone from the Whois directory, as well as resource databases and other similar data sources.
User context data
This type of data includes all information relating to the management of users and their identity. Also included are Active Directory, Centrify and other similar systems.
Endpoint context data
Includes all information about endpoint systems (server, router, switch). They can come from asset management systems, vulnerability scanners and detection systems.
Contextual threat data
This data contains contextual information on URLs, domains, websites, files and much more, always related to known threats.
Contextual data on vulnerabilities
This data includes information on vulnerabilities and vulnerability management systems.
Articles from the RoadMap
This is file context data, certificates, naming convention.

Name of attributes
A naming convention is required for an Open Data Model in order to represent attributes between the vendor’s products and technologies. The naming convention consists of prefixes (net, http, src, dst, etc) and common attribute names (ip4, usarname, etc).
It is still a good idea to use multiple prefixes in combination with one attribute.
Conclusions
We have seen what the Hadoop Open Data Model is and how it can be used thanks to its ability to filter traffic and highlight potential cyber attacks by listing suspicious flows, threats to users, threats to endpoints and major network threats.
If you have any doubts or would like further clarification, do not hesitate to contact us by pressing the button below, we will be happy to answer any question.
Useful links:

Estimated reading time: 5 minutes
Every year the number of attacks that threaten the security of devices, computer systems, servers and network infrastructures is growing steadily. This is done by taking advantage of the vulnerabilities present in these systems. Among the many types of attacks, particular attention must be paid to the pass the ticket (PTT) attack.
With a pass the ticket attack it is possible to take advantage of the Kerberos network protocol, present in all major operating systems, to access a user’s session without having his login credentials. An attack of this type can be difficult to detect and is usually able to bypass the most common system access controls.

Pass The Ticket: what it is and how it works
Kerberos
Before understanding in detail what a PTT attack is and how it works, it is advisable to clarify the Kerberos network protocol since an attack of this type uses this protocol. Kerberos is a network protocol designed by MIT in the 1980s and became a standard IETF in 1993. It is used for strong authentication between different terminals through a symmetric key encryption system, without transmitting any passwords.
The advantage of using the Kerberos protocol lies in its strong authentication system between client and server. This makes it very effective against phishing and “ man in the middle ” attacks.
Kerberos is integrated into all major operating systems belonging to well-known companies such as Microsoft, Apple, Red Hat Linux and many more.
With a pass the ticket attack it is possible to exploit Kerberos authentication to gain access to a user account. The consequences that such an event could entail are not are to be underestimated. Among the many imaginable scenarios, for example, there could be the possibility that the compromised account enjoys high administrative privileges thus guaranteeing the hacker full access to resources.
The attack
A pass the ticket attack allows you to gain privileged access to network resources without having to use any user passwords . Here’s how: In Active Directory, a Ticket Granting Ticket (TGT) serves to prove that a user is just who he says to be. Through some tools and techniques, a hacker could collect these tickets and use them to request Ticket Granting Services (TGS) in order to access resources present in other parts of the network.
A PTT attack could involve risks even if the compromised account does not have particular administrative privileges since the hacker, through the Lateral Movement, may be able to gain access to other accounts and devices.
The difference between pass the ticket and an attack pass the hash lies in the fact that the former exploits TGT tickets that have an expiration of a few hours, while the latter uses NTLM hashes that change only in case a user decides to change his password. A TGT ticket must be used within its expiration time or renewed for a longer period of time.
How to Defend and Prevent a Pass The Ticket Attack
Keeping a network and the devices connected to it safe is a very important factor. You must always have protocols and software that are able to guarantee effective protection from all kinds of threats , with up-to-date systems that keep sensitive information safe. Enterprises can take advantage of endpoint detection and response technologies. Local detection of multiple tickets used for the same session will be possible.
Account case without-privileges
In the event of a pass the ticket attack, if the compressed account from which the TGT or TGS was stolen was a low-privilege account, the mitigation could be quite simple. Just reset the user’s Active Directory password. Such an action would invalidate the TGT or TGS, preventing the hacker from generating new tickets.
Case-account with privileges
Conversely, if the PTT attack compromised a privileged account, limiting the damage is much more difficult. In these cases, companies could respond to the attack by resetting the Kerberos TGT service to to generate a new signing key, making sure to delete the compromised key.
Next you need to drill down into Kerberos logs and Active Directory information to investigate and find out which network resources have been compromised. In this way it is also possible to understand which data may have been stolen. The technology SIEM allows organizations to assimilate, analyze and analyze this data.

Protection from attack
To ensure complete protection of an infrastructure, also preventing pass the ticket attacks, it is good to use valid detection technologies such as UEBA and SIEM. In fact, it is possible to prevent Pass The Ticket attacks by analyzing the behavior of users and entities. The solution UEBA , in these cases, would ensure the quick identification of any compromised account, blocking it in order to mitigate the damage.
Some software SIEM also allow not only to analyze traditional logs but are also able to provide an accurate analysis of security , analyzing the behavior of the network and users in order to detect promptly the presence of any threats to the infrastructure.
Conclusions
We have seen what a pass the ticket attack is and how companies can adopt specific solutions to intercept the dangers and anomalies of an entire IT infrastructure. This allows us to mitigate threats more effectively.
A complete solution, as we have seen, involves constant and granular communication monitoring . The solution we propose for this purpose is a SOCaaS .
If you want to know our dedicated security services, do not hesitate to contact us. You can use the button below, we will be happy to answer any of your questions.
Useful links:

Estimated reading time: 5 minutes
In the previous article we have seen the most common use cases of a SOCaaS , explaining how it can be useful for companies to use this tool to prevent cyber attacks and also explaining which are the most common Threat Models .
In this article, however, we will take a closer look at some of the more common indicators of compromise (IOC). First we will briefly look at the malware threat models that the use of a SOCaaS can prevent and block. As it works, a SOCaaS can be very flexible and analyze a lot of data at the same time, thus providing in-depth and accurate results.

Malware Threat Models
It is important to know how to distinguish and classify the different types of malware to understand how they can infect systems and devices, the level of threat they represent and how to protect against them. We at SOD recommend adopting the use of a SOCaaS in order to be able to classify the entire range of malware or potentially unwanted objects. Malware is categorized based on the activity they perform on infected systems.
Wannacry Malware Detection
Thanks to this threat model it is possible to detect the behavior of the well-known malware Wannacry.
Wannacry malware is a ransomware that attacks the system by encrypting files of particular importance to an organization in order to make them illegible.
Early detection of ransomware is probably the most effective action you can take to defend yourself. There are also services that are able to block the action of the malware and restore any files already encrypted with those of a backup, for example Acronis Cyber Protect Cloud .
Network anomaly followed by data infiltration
Identifies successful network data aggregation attempts, followed by signs of data infiltration. Below we see some of the anomalies and how the use of a SOCaaS can identify important clues to counter threats.
During a network scan you may notice enumerations of AD accounts and privileges, count of LDAP services outside the corporate network and a suspicious number of ticket requests to Kerberos protocol . In addition, other indicators can be a spike in LDAP traffic and the enumeration of SMB services.
As regards the anomalies of the network drive , the use of a SOCaaS is able to control access to the sharepoint in order to identify an unusual number of accesses to shared elements. This also in relation to users and their level of access.
In terms of Data Aggregation and data infiltration, the quantity of bytes downloaded from the server ports and via FTP protocols are monitored, as well as an unusual quantity of bytes transmitted to the external.
Petrwrap / Goldeneye / Amalware detection
This threat model aims to detect malware Petrwrap . The use of a SOCaaS can detect network scanning activity by monitoring the number of SMBv1 activities, as well as anomalies in these activities. Attempting to reach a never-before-reached host may also be an indicator.
Another way in which these threats can be detected with the use of SOCaaS is by auditing of suspicious privileged activity. For example, it is verified that there is no escaletion of privileges, unusual access to an admin zone or even tampering with log files.
Risk indicators in general
Risk indicators are metrics used to show that the organization is subject to or has a high probability of being subject to a risk.
These indicators are used to classify the type of behavior or threat for a policy and can be used in multiple policies for different functionality based on the data source. Risk indicators can be chained with threat models to identify sophisticated attacks across multiple data sources.
In essence, these are clues or alarm bells that indicate events that a company’s security operators should pay particular attention to. The use of a SOCaaS can help identify these clues by analyzing large amounts of data and logs in a short time.
Below is a non-exhaustive list of some of the most common threat indicators that are identifiable through the use of a SOCaaS. We will divide them into different areas, for clarity.
As for accounts, obviously, blocking an account is an alarm bell, as well as an unusual number of accounts created or a disproportionate number of failed authentication. Finally, the use of a SOCaaS could indicate an IOC as a suspicious number of accounts running concurrently .
Access
The anomalies concerning the access or in any case the account include the detection of access to the anomalous administrative sherepoint but also the loading times of the anomalous applications. Applications that use an unusual amount of memory may also be indicators of compromise.
As for accounts, obviously, blocking an account is an alarm bell, as well as an unusual number of accounts created or a disproportionate number of failed authentication. Finally, the use of a SOCaaS could indicate an IOC as a suspicious number of accounts running concurrently .

Networks
Network alarm bells are, of course, the most common. Since networks are like “roads” of a corporate infrastructure, it is normal that anomalous behaviors in these are particularly relevant.
Common indicators are abnormal DNS zone transfers or failed requests to the firewall. But also an abnormal number of running hosts or ICMP connections. Traffic in general is also controlled through the use of SOCaaS, so that any suspicious data movement is analyzed or otherwise verified. Examples of this are packet movements to critical ports, RDP, SSH, or connection attempts to a DHCP server. These events often indicate abnormal attempts to connect to objects or network shares.
Through the use of a SOCaaS it is also very simple to control the behavior of the accounts that often show alarm bells in themselves . For example, an account logging into a host for the first time, creating an account, or adding privileges.
Conclusions
Relying on luck to catch threats is madness , as demonstrated by SolarWinds attack .
Create your luck with our SOCaaS solution , making sure you spot threats before incidents happen and that you are “lucky” enough to counter them.
Contact us to find out how our services can strengthen your company’s defenses, we will be happy to answer any questions.
Useful links:

Estimated reading time: 6 minutes
Cyber Threat Analytics applications monitor security logs and the network to promptly detect any malware infections (for example, attacks zero day e i ransomware), the compromise of the system, the activities of “ lateral movement ”, pass-the-hash , pass-the-ticket and other advanced intrusion techniques. The use of a SOCaaS allows to extrapolate data from sources such as firewalls, proxies, VPN, IDS, DNS, endpoints, and from all devices connected to the network with the aim of identifying harmful models such as “beaconing”, connections to generated domains digitally, actions performed by robots and all anomalous behaviors.
Our system SOCaaS is equipped with artificial intelligence that enriches and transforms events SIEM, so you identify threats across your entire IT environment, including business-critical applications.
What are the-advantages at the enterprise-level?
The use of a SOCaaS. Below is a list with only some of the advantages that the use of SOCaaS can entail rapid detection of violations, reducing the impact of these. Additionally, a SOCaaS provides comprehensive threat responses and investigations, decreases monitoring and management costs, as well as compliance costs.
The use of a SOCaaS also allows you to receive quantified and non-subjective reports on threats and risks.

SOCaaS use cases
After a general overview of the advantages that the use of SOCaaS could offer to the company, let’s see in what contexts it is normally used .
A SOCaaS consists of elements that are very suitable to be applied in case of abnormal execution of applications, as well as in the analysis of bot traffic to a malicious website.
In other cases, SOCaaS identifies unusual DNS queries, a possible remote command and control activity, analyzes the spikes in bytes to external destinations and then also checks the traffic, relating it in an application / port context.
Other scenarios in which the use of SOCaaS is ideal are the detections of exploits, sessions of unusual duration, but also connections to IPs or blacklisted domains and anomalous activity in general.
Finally, it can also detect targeted SPAM attacks and phishing attempts.
Threat Models
By analyzing threat indicators it is possible to detect correlated behaviors on multiple data sources, to also detect all those threats that usually go unnoticed. Multiple threat indicators occurring in a scheme and involving similar entities tend to present a greater risk of posing a real threat.
The Threat Models define these patterns and combine threat policies and indicators to detect related behaviors across multiple data sources, identifying threats that may go unnoticed. Below are some of the more common Threat Models that are included in the use of a SOCaaS
Lateral Movement Detection
This Threat Model detects the possible scenarios of “ lateral movement “, used by attackers to progressively spread across a network in search of key resources and data. The signs of such an attack can be varied and we can divide them into three categories: Abnormal authentication, suspicious privileges, abnormal process.
Abnormal authentication is usually detectable by some clues. For example if an account accesses a host that has never been reached before. Or if explicit credentials are used on multiple hosts, or if a suspicious authentication type / process is detected.
Concerning suspicious privileges, here are some indicators detectable with the use of a SOCaaS:
- abnormal provisioning activity
- suspicious escalation of privileges
- abnormal access to network share objects
An abnormal process is detected in this way through the use of a SOCaaS: an unusual process code, or the suspicious creation of scheduled tasks. Alternatively, suspicious changes to the registry settings may be detected.
Detection of compromised hosts
This model is employed in the use of SOCaaS to detect hosts showing signs of infection and compromise by relating host and network based anomalies to the same entity.
A possible alarm is given by anomalies in outgoing traffic . This occurs when traffic goes to random domains or known malicious hosts. In other cases, however, an abnormal number of domains contacted is another alarm bell detectable through the use of a SOCaaS.
anomalies in the endpoint are found when rare processes or suspicious use of ports or protocols by the process itself are found. One possibility is also to detect an unusual agent.
APT detection using a SOCaaS
Detection APT detects attacks on health care networks , where the attacker’s aim is usually to obtain a unauthorized access to a network with the intention of remaining undetected for an extended period.
This includes phishing attempts , detection of a network scan or circumvention of controls. In the delivery phase, however, traffic to random domains, an anomaly in DHCP traffic or traffic destined to known malicious hosts may be identified.
During an exploit , the indicators can be: the detection of activity from terminated accounts, anomalous DNS traffic, but also a suspicious authentication process. Another possible indicator identifiable with the use of SOCaaS is an anomaly in the speed of the network.
Through the use of a SOCaaS, cases of data exfiltration can also be detected. The signals in this case are l ‘Unauthorized upload of data over the network.
Detection model Phishing using SOCaaS
This model is able to detect possible phishing attempts towards users within the organization . We’ve talked about it in other articles as well, and here are some indicators of this type of attack. A wake-up call is definitely the detection of known phishing campaigns. It is also not uncommon for spear phishing attacks to be detected.
The use of a SOCaaS is also able to identify possible phishing attempts or persistent phishing campaigns, thanks to the comparison with emails from senders / domains / IP addresses known in the blacklists. As usual, beware of suspicious email attachments, but the use of a SOCaaS could automate, at least in part, the checks.
It is then possible to identify outbound traffic anomalies , for example that towards random domains, which is also a possible phishing signal. Classic traffic to malicious hosts, an abnormal number of rare domains accessed, can also be indicators.

Host / Account Enumeration on LDAP
Usually used to identify potential assets or account enumerations on the network by malicious entities.
Running suspicious processes
- Abnormal process / MD5 detected
- Use of possible sets of AD (Active Directory) enumeration tools
- Detected use of malicious tools and utilities
Network scanning
- Possible AD accounts / enumeration privileges
- LDAP or SMB service count
- Abnormal number of Kerberos service ticket requests
- Port scanning
Authentication anomalies
- Accounts accessing a host for the first time
- Using never-before-seen accounts on the network
- Abnormal number of failed authentication requests
Reconnaissance followed by potential exploitation
This threat model aims to identify successful network reconnaissance attempts, followed by indicators of exploitation.
External scanning
- Scanning ports from external hosts
- Enumerating hosts from external hosts
Network scanning
- Possible count of AD accounts / privileges
- Enumeration of LDAP services
- Unsolved number of Kerberos service ticket requests
- Spikes in traffic LDAP
- Enumeration of SMB services
Anomalies in processes
- Detection of abnormal processes or MD5
- Suspicious creation of scheduled tasks
- Suspicious changes to registry settings detected
Conclusions
We have seen what are the major SOCaaS use cases, taking a look at some of the most common threat models that it includes in its protection system. For information on malware threat patterns and threat identifiers visit this article.
Using a SOCaaS is a solid and highly valuable business solution, ask us what it can do for your business, we will be happy to answer any questions.
Useful links:

Il NIST Cybersecurity Framework è un insieme di linee guida sviluppato per ridurre i rischi legati alla sicurezza informatica. Elenca delle attività specifiche associate alla gestione del rischio di sicurezza informatica basandosi su standard e linee guida già esistenti. È uno dei più popolari framework dedicati alla sicurezza informatica ed è impiegato in modo diffuso perché fornisce un aiuto sotto l’aspetto della gestione del rischio.
Redatto dal National Institute of Standards and Technology (NIST), questo quadro di cybersecurity affronta la mancanza di standard quando si tratta di cybersecurity. Infatti, fornisce un insieme uniforme di regole, linee guida e standard per le organizzazioni da utilizzare nei vari settori. Il NIST Cybersecurity Framework (a volte abbreviato NIST CSF) è ampiamente considerato come il gold-standard per costruire un programma di cybersecurity.
Sia che tu abbia appena iniziato a stabilire un programma di cybersecurity o che tu stia già eseguendo un programma abbastanza maturo, il framework può fornire valore aggiunto. Agisce come uno strumento di gestione della sicurezza di alto livello che aiuta a valutare il rischio di cybersecurity in tutta l’organizzazione.

La struttura del NIST Cybersecurity Framework
Il NIST Cybersecurity Framework è strutturato principalmente in tre parti:
Core: contiene una serie di attività, risultati e riferimenti su aspetti e approcci legati alla sicurezza informatica.
Implementation Tiers: è un sistema di classificazione che aiuta le organizzazioni a fare chiarezza sugli aspetti dedicati alla gestione del rischio di sicurezza informatica.
Profile: in sostanza è l’elenco dei risultati che un’organizzazione ha scelto, in base alle proprie necessità, dalle categorie e sotto-categorie della struttura.
Funzioni e categorie delle attività di cybersecurity
Il Core del NIST possiamo dividerlo in 5 sezioni, che a loro volta sono suddivise in 23 categorie. Per ogni categoria si definisce una serie di sotto-categorie, per un totale complessivo di 108 sotto-categorie. Ogni sotto-categoria, fornisce delle Risorse informative che fanno riferimento a sezioni specifiche di altri standard di sicurezza, come ISO 27001, COBIT, NIST SP 800-53, ANSI/ISA e CCS CSC.
La complessità di questo framework, ha dato origine alla creazione di progetti di legge che guidano il NIST a creare delle linee guida facilmente accessibili alle piccole e alle medie imprese.
Sezioni del NIST Cybersecurity Framework
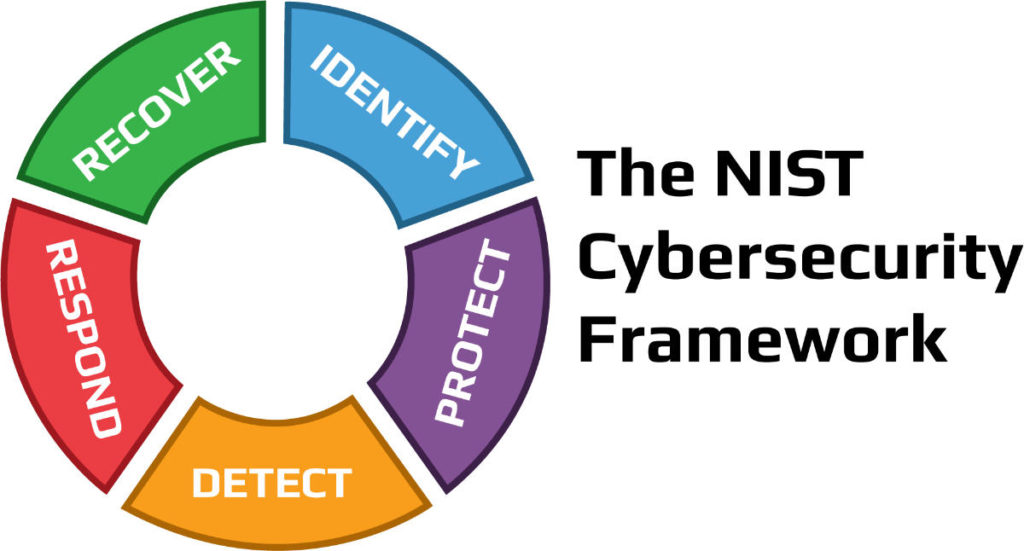
Identificazione (Identify)
La funzione di identificazione si concentra sul porre le basi per un efficace programma di cybersecurity. Questa funzione assiste nello sviluppo di una comprensione organizzativa per gestire il rischio di cybersecurity per sistemi, persone, beni, dati e capacità. Per consentire a un’organizzazione di concentrare e dare priorità ai suoi sforzi, coerentemente con la sua strategia di gestione del rischio e le esigenze di business, questa funzione ha sottolineato l’importanza di comprendere il contesto di business, le risorse che supportano le funzioni critiche, e i relativi rischi di cybersecurity.
Le attività essenziali in questa sezione del NIST includono:
Individuare le risorse fisiche e software per stabilire la base di un programma di gestione delle risorse
Definire l’ambiente di business dell’organizzazione, compreso il suo ruolo nella catena di fornitura
Scegliere le politiche di cybersecurity stabilite per definire il programma di governance e identificare i requisiti legali e normativi relativi alle capacità di cybersecurity dell’organizzazione
Identificare le vulnerabilità degli asset, le minacce alle risorse organizzative interne ed esterne e le attività di risposta al rischio per valutare il rischio
Stabilire una strategia di gestione del rischio, compresa l’identificazione della tolleranza al rischio
Produrre una strategia di gestione del rischio della catena di fornitura, comprese le priorità, i vincoli, le tolleranze di rischio e le ipotesi usate per sostenere le decisioni di rischio associate alla gestione dei rischi della catena di fornitura
Protezione (Protect)
La funzione di protezione del NIST delinea salvaguardie appropriate per garantire la fornitura di servizi di infrastrutture critiche. Inoltre, supporta la capacità di limitare o contenere l’impatto di un potenziale evento di cybersecurity.
Le attività critiche in questo gruppo includono:
Implementare le protezioni per la gestione delle identità e il controllo degli accessi all’interno dell’organizzazione, compreso l’accesso fisico e remoto
Responsabilizzare il personale attraverso la formazione sulla consapevolezza della sicurezza, compresa la formazione degli utenti privilegiati e basata sui ruoli
Stabilire una protezione della sicurezza dei dati coerente con la strategia di rischio dell’organizzazione per proteggere la riservatezza, l’integrità e la disponibilità delle informazioni
Implementare processi e procedure per mantenere e gestire le protezioni dei sistemi informativi e delle risorse
Proteggere le risorse organizzative attraverso la manutenzione, comprese le attività di manutenzione a distanza
Gestire la tecnologia per garantire la sicurezza e la resilienza dei sistemi, coerentemente con le politiche, le procedure e gli accordi organizzativi
Rilevamenti (Detect)
Rilevare potenziali incidenti di cybersecurity è fondamentale e questa funzione del Framework definisce le attività appropriate per identificare il verificarsi di un evento di cybersecurity in modo tempestivo. Le attività in questa funzione includono:
Garantire il rilevamento di anomalie ed eventi e la comprensione del loro potenziale impatto
Implementare capacità di monitoraggio continuo per monitorare gli eventi di cybersecurity e verificare l’efficacia delle misure di protezione, comprese le attività di rete e fisiche
Risposte (Respond)
La funzione di risposta del NIST si concentra sulle attività appropriate per agire in caso di un incidente di cybersecurity rilevato e supporta la capacità di contenere l’impatto di un potenziale incidente di cybersecurity.
Le attività essenziali per questa funzione includono:
Garantire l’esecuzione del processo di pianificazione della risposta durante e dopo un incidente
Gestire le comunicazioni con gli stakeholder interni ed esterni durante e dopo un Analizzare l’incidente per Garantire una risposta efficace e sostenere le attività di recupero, compresa l’analisi forense e la determinazione dell’impatto degli incidenti
Eseguire attività di mitigazione per prevenire l’espansione di un evento e per risolvere l’incidente
Implementare miglioramenti incorporando le lezioni apprese dalle attività di rilevamento/risposta attuali e precedenti
Recupero (Recover)
La funzione recupero del framework identifica le attività appropriate per rinnovare e mantenere i piani di resilienza e per ripristinare qualsiasi capacità o servizio che sia stato compromesso a causa di un incidente di cybersecurity. Il recupero tempestivo alle normali operazioni è importante per ridurre l’impatto di un incidente.
Le attività essenziali per questa funzione si sovrappongono in qualche modo a quelle di risposta e includono:
Assicurare che l’organizzazione implementi processi e procedure di pianificazione del recupero per ripristinare i sistemi e/o gli asset colpiti da incidenti di cybersecurity
Implementare miglioramenti basati sulle lezioni apprese e sulle revisioni delle strategie esistenti
Le comunicazioni interne ed esterne sono coordinate durante e dopo il recupero da un incidente di cybersecurity
Come iniziare con il NIST Cybersecurity Framework
Allinearsi con il framework significa enumerare tutte le vostre attività ed etichettare questi elementi con una di queste 5 etichette di funzione. Per esempio, l’etichetta Identify sarà per gli strumenti che vi aiutano a inventariare le vostre risorse. Strumenti come Firewall andranno in Protect. Tuttavia, a seconda delle loro capacità, li potreste voler mettere anche in Detect insieme ai vostri SIEM. Gli strumenti di risposta agli incidenti e i playbook vanno in Respond. I vostri strumenti di backup e ripristino fanno parte di Recover.
Una volta che avete fatto questo esercizio, alcune delle sezioni potrebbero sembrare più vuote di altre e potreste sentirvi a disagio per la descrizione della funzione corrispondente.
Questo è un bene, perché ora potete articolare ciò che manca al vostro programma di cybersecurity.
Conclusioni
In questo articolo abbiamo compreso cos’è il NIST Cybersecurity Framework e come è strutturato analizzando alcune delle sue sezioni principali e degli elementi che compongono queste sezioni.
Tuttavia, il nostro consiglio è quello di rivolgervi a un provider SaaS che vi possa fornire gli strumenti per implementare il NIST in modo efficiente senza alcun rischio. Le nostre soluzioni SaaS possono aiutare in questo senso e invitiamo a contattarci per sapere come i nostri servizi possono aiutare la tua azienda in ambito di sicurezza informatica.
Non esitare a contattarci per saperne di più, risponderemo a ogni vostra domanda.
Useful links:

Tempo di lettura stimato: 7 minutes
Quando parliamo di “left of boom” o “right of boom” ci riferiamo ad un concetto che all’apparenza può sembrare superficiale. Invece, è un potente strumento che offre la possibilità di analizzare i conflitti di sicurezza sia da un punto di vista offensivo che da uno difensivo. In una ipotetica linea temporale di un attacco, ciò che si trova alla sua sinistra (left of boom) si riferisce a quello che accade prima. Analogamente, ciò che sta alla destra, è quello che avviene dopo.
Nel linguaggio comune molto spesso anziché “boom” si utilizza il termine “bang”, ma il significato resta comunque invariato. Si tratta, in sostanza, dell’evento stesso intorno al quale si analizza il periodo precedente e successivo.
Quindi, “left of boom” è l’insieme di eventi che si verificano prima dell’attacco. “Right of boom”, invece, è l’insieme di eventi che seguono il “boom”. Questa è la differenza sostanziale tra i due termini. Se le azioni difensive riescono a rilevare gli eventi nel periodo “left of boom”, è possibile trovare e adottare soluzioni per prevedere quando accadrà il “boom”.
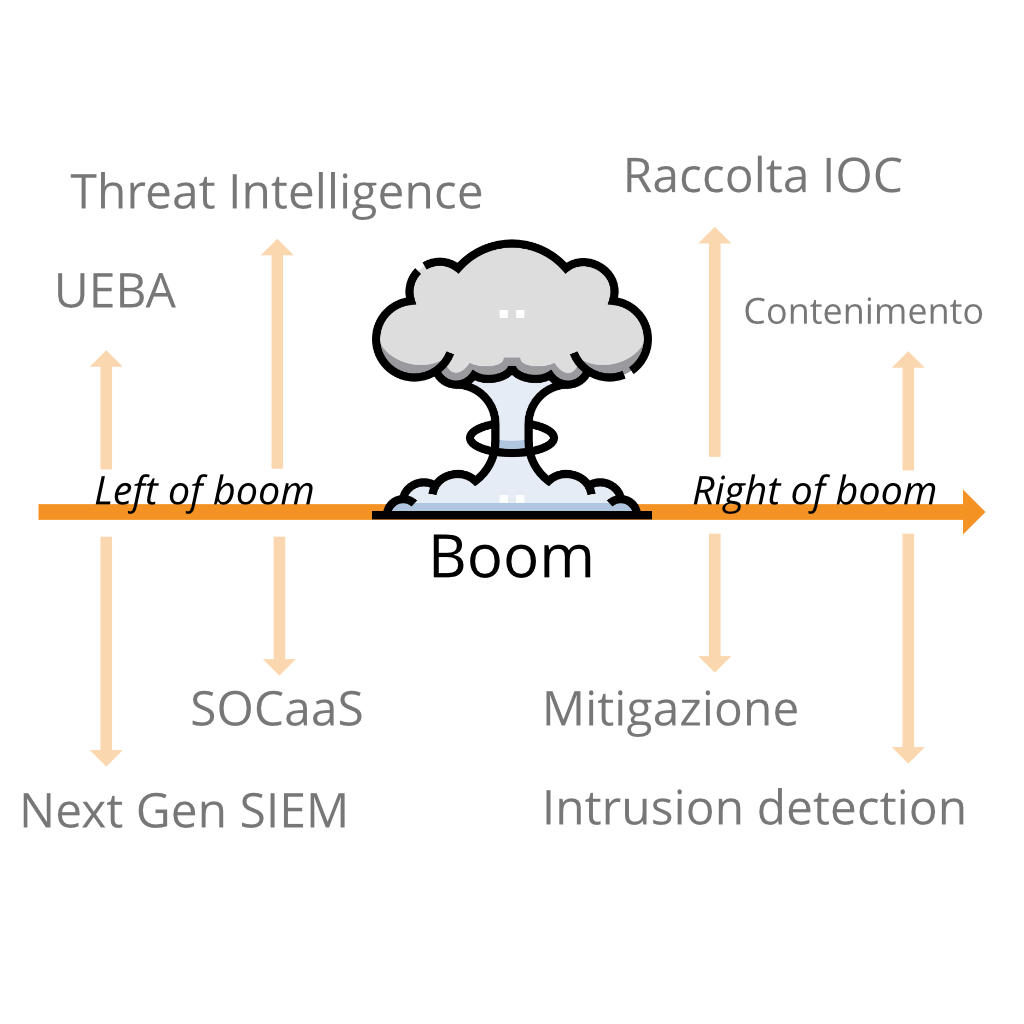
Per una persona inesperta nell’ambito della sicurezza informatica, questi concetti riguardanti la linea temporale di un attacco informatico potrebbero non essere nemmeno presi in considerazione, per questo motivo molte aziende preferiscono avvalersi di un SOCaaS.
Left of Boom
Un buon penetration tester riesce a rilevare alcuni eventi di tipo “left of boom”, ma spesso si tralascia la raccolta di informazioni sulle minacce. Certe volte non è in grado di distinguere tra loro concetti come “ingegneria della sicurezza, scoperta e risoluzione delle vulnerabilità” da un “controllo di prevenzione automatizzato”.
Non esiste in realtà un vero strumento valido di prevenzione, più che altro i controlli di sicurezza sono controlli di rilevamento. Alcuni di questi controlli integrano dei meccanismi di risposta automatizzati che impediscono il susseguirsi di spiacevoli eventi.
Un’applicazione web che previene attacchi di tipo XSS o SQLI è davvero utile per rilevare input non validi e risponde scartando il contenuto prima che l’iniezione possa verificarsi.
Un firewall progettato per bloccare le porte rileva semplicemente il traffico indesiderato in relazione al protocollo usato per la connessione e al numero della porta verso la quale si desidera accedere, interrompendo e reimpostando la richiesta di connessione.
Questi esempi si legano bene al concetto di “right of boom”. I controlli di prevenzione rilevano il “boom”, l’evento, e rispondono immediatamente arginando i possibili danni. “Left of boom” e “right of boom” sono così vicini nella linea temporale che sono difficilmente distinguibili, fino a quando non si esegue un’analisi accurata degli eventi.
Questo è uno dei motivi per cui i professionisti, nell’ambito della sicurezza informatica, amano i controlli di prevenzione. Lavorano rapidamente per correggere gli errori prima che gli hacker riescano a raggiungere i loro obbiettivi, limitando i danni.
Un SOCaaS in questi casi è una delle soluzioni migliori da adottare per proteggere l’integrità di un sistema informatico.
Right of Boom
Generalmente minore è la distanza tra “right of boom” e il tempo di risposta ad una minaccia, minori sono le conseguenze provocate da un eventuale attacco informatico. Ovviamente questa è solo una considerazione logica, non vale come regola assoluta.
Per alcune violazioni, la linea temporale tra l’evento e l’eliminazione completa della minaccia è discutibile, poiché il rilevamento è avvenuto dopo che l’hacker ha raggiunto il suo obbiettivo. Se gli hacker riescono ad infiltrarsi nel sistema ma vengono fermati in tempo, non arrecando nessun danno all’infrastruttura. In questo secondo caso, quindi, non c’è il “boom” di cui stiamo parlando.
Un esempio di right of boom
Per spiegare meglio il concetto di “right of boom” potremmo prendere come esempio un comune “malware”. I malware generalmente vengono sviluppati per attaccare in massa molti dispositivi, senza tanta discrezione. Con “right of boom” ci riferiamo a quel periodo di tempo che è passato da quando è avvenuta l’infezione da parte del malware.
Se hai letto gli altri articoli pubblicati da noi avrai appreso come gli hacker utilizzano queste tipologie di infezioni allo scopo di raccogliere informazioni sensibili, che vengono rivendute ad un terzo soggetto. Se il “right of boom” è più breve del tempo che l’hacker impiega per vendere queste informazioni, il danno può essere contenuto.
I migliori sistemi di sicurezza riescono ad accorciare il tempo “right of boom” riuscendo a raccogliere informazioni sugli attaccanti nel “left of boom”. Ci si può riuscire implementando delle contromisure in base al modello di minaccia. Questi strumenti permettono di scansionare intere infrastrutture, osservando i nuovi indicatori di minaccia giorni o addirittura settimane prima che gli attacchi si distribuiscano.
Come abbiamo visto anche in altri articoli, non sempre gli attacchi si svolgono in breve tempo. È, anzi, più probabile che gli hacker coinvolti agiscano in un primo, lento, periodo solo per raccogliere le informazioni necessario per sferrare l’attacco. Nel periodo “right of boom”, tornano utili strumenti come la cyber threat intelligence e un team di threat hunting.

Perché sono importanti i concetti “Right e Left of boom”
Se ci mettessimo nell’ottica dell’hacker, il concetto di “right of boom” e di “left of boom” può aiutare a decidere quale schema d’azione sia meglio intraprendere.
Supponiamo il caso in cui un hacker abbia a disposizione due metodi per potersi introdurre in un sistema informatico. Se uno dei due metodi potrebbe venire rilevato nel periodo “left of boom”, invece l’altro nel “right of boom”, è ovvio che l’hacker preferirà il secondo. Infatti, questo garantirebbe maggiori probabilità di successo dell’attacco.
Analogamente, tra due metodi che possono essere rilevati “right of boom” si sceglie quello che ha più possibilità di venir scoperto in ritardo. Più tempo passa dal boom alla rilevazione, maggiori sono le probabilità di successo. Questo tipo di ragionamento è importante per determinare quale tattica ha una linea temporale più ampia.
Ragionare in quest’ottica non è affatto semplice, richiede delle conoscenze avanzate da parte dell’esperto di sicurezza. Richiede inoltre il dover prendere in considerazione tutte quelle ipotesi che potrebbero potenzialmente determinare il successo dell’hacker.
Velocità
Un hacker è in grado di riuscire a prevedere se, utilizzando determinate tattiche, riuscirebbe a raggiungere l’obbiettivo più velocemente rispetto all’esperto che cerca di rilevare gli attacchi. Il “boom” è il primo contatto, nell’insieme delle tattiche d’intrusione utilizzate per accedere illegalmente ad un sistema informatico. Le rimanenti tattiche si collocano prima e dopo di esso.
Velocità e furtività solitamente si annullano a vicenda. Infatti, molto spesso si può essere più veloci sacrificando parte della furtività.
Velocità e furtività non vanno molto d’accordo quando parliamo di attacchi informatici. Essere furtivi, evitando di lasciare tracce, richiede più attenzione e quindi inevitabilmente anche più tempo. Tuttavia se lo scopo di un hacker non è un singolo obbiettivo ma una serie di più obbiettivi, l’essere veloci può rivelarsi efficace.
Per difendersi dagli attacchi, è possibile raccogliere gli indicatori di compromissione (IOC) per rimediare alle vulnerabilità presenti e per introdurre nuovi controlli di rilevamento, rendendo più sicuro il sistema informatico.
Conclusioni
È importante conoscere il concetto di linea temporale degli attacchi e abbiamo visto come i concetti di “left of boom” e “right of boom” influenzino i meccanismi di risposta alle minacce di intrusione.
I concetti che abbiamo visto in questo articolo, nonostante non aggiungano niente di concreto alle tecniche di difesa o di attacco di un sistema, offrono un punto di vista. Nella continua lotta tra hacker e operatori di sicurezza, avere una strategia vincente significa non solo disporre di strumenti efficienti, ma anche pianificare in modo dettagliato ogni dettaglio, prima e dopo gli attacchi.
Per sapere come un SOCaaS può aiutarti a monitorare l’infrastruttura aziendale e cogliere gli indizi “left of boom”, non esitare a contattarci, sapremo rispondere a ogni domanda e ti offriremo una soluzione per la tua azienda.
Useful links:

Estimated reading time: 4 minutes
Today, facing an attack in a corporate SOC is very similar to being under attack without knowing which direction the blow is coming from. The threat intelligence can keep you informed of security issues. However, in many cases, this information is only provided when you are already under attack, and is rarely very useful except in retrospect. It would take a different approach to data analysis, and that’s exactly what we propose with predictive cybersecurity .
In cybersecurity, threat intelligence is still relied upon as a fundamental defensive tool. Unfortunately, threat intelligence only covers a subset of threats that have already been found, while attackers constantly innovate . This means that new malware executables, phishing domains and attack strategies are created all the time.
Threat intelligence has a strong value for reactive incident response. It helps when pivoting through an investigation, identifying intent or other useful data, and providing additional investigative assistance. But it has limited value for detection, as threat actors avoid reusing their attack infrastructure from one target to another.
If the clues you see are different from those known from previous attacks, what can you do to move forward with effective detection? A legitimate question, for which predictive cybersecurity perhaps has an answer.
… what if you could know what is going to hit?
SOCaaS: predictive cybersecurity
Eyes on opponents rather than past attacks
The SOCaaS solution offered by SOD brings predictive cybersecurity capabilities to cybersecurity. The solution maps adversaries , instead of threats, and analyzes their actions to predict the behavior and the tools used in their attacks.
The analytical engine translates behavioral patterns into profiles of adversary attack infrastructures , which indicate as ( trojan, phishing or other forms of attack ) and where ( branches, customers, partners, peers, industry and geographies ) < strong> attackers are planning to target your company .
This provides a preemptive attack map, which identifies opponents based on their attack phase and current position within the extended business landscape . But not only that, in fact, information about the opponent, typical attack patterns and possible countermeasures that can be taken in advance are also identified. This way you can cancel the threat before it materializes .

Predictive cybersecurity: understand what’s going to happen first
Our SOCaaS provides predictive detection capabilities against internal and external threats with the combination of user, entity and adversary behavior analysis. Our Next-Gen SIEM uses an analytics-driven approach to threat detection. SOC provides visibility in the crucial early stages of an attack. That is when cyber actors are targeting, planning and preparing the infrastructure for an attack.
With this level of predictive visibility, the team can prevent attacks and systematically contain those in progress. Predictive cybersecurity allows defenders to tune their systems against the attack infrastructure. In fact, it is possible to build blacklists that include the IP addresses and the host names of the instances used for the attack . Other measures include fortifying corporate systems against the specific malware that is used to target them, rendering the attack powerless when it occurs.
Opponent Behavior Analysis extends the capabilities of Next-Gen SIEM by continuously providing updated analysis of opponent information and behavior . This encompasses the entire attack infrastructure for dynamic and proactive threat protection.
SOCaaS automatically translates the pre-attack behavior of opponents into actions or countermeasures that can be taken against phishing, compromise of corporate email, ransomware, fraud and many other common threats.
Common use-cases
Threat-chaining
Correlate breaches from the same adversary / campaign into a cohesive threat, even if different pieces of attack infrastructure are used for each event.
Prevention and preventive defense
Preemptively blocking an opponent’s entire attack infrastructure, such as newly created phishing domains, for preemptive defense.
Strengthen vulnerable resources
Focus and secure the most vulnerable parts of your infrastructure based on information that identifies which areas are possible targets.

The information provided by SOCaaS is used to add more context to existing threats, as well as provide information on attacks that have not yet been implemented or are in the early stages, such as reconnaissance. This allows for direct action against evolving threats and a more robust defense.
Conclusions
Relying on luck to catch threats is madness, as the recent SolarWinds attack . Make your fortune with SOD’s SOCaaS solution, making sure you see threats before they happen and are “lucky” enough to counter them.
Useful links:

Estimated reading time: 8 minutes
The term shoulder surfing might conjure up images of a little surfer on his shirt collar, but the reality is much more mundane. shoulder surfing is a criminal practice in which thieves steal your personal data by spying on you while using a laptop, ATM, public terminal or other electronic device among other people . This social engineering technique is a security risk that can cause disaster, especially if the stolen credentials are corporate.
The practice long predates smartphones and laptops and dates back to when criminals spied on pay phone users as they entered their calling card numbers to make calls . Many years have passed, but the technique has not been lost. Thieves have evolved to observe their victims typing their ATM PINs, paying at self-service petrol pumps, or even making a purchase in a store.
A similar technique for ATM theft involves a card cloning device superimposed on the card insertion hole and a micro camera to spy on the code. The micro camera performs an act of shoulder surfing . Card cloning is essential because without a physical device the pin is useless, but in the case of account credentials on the network, all you need is user and password.

When does Shoulder Surfing take place?
shoulder surfing can happen whenever you share personal information in a public place. This includes not only ATMs, coffee shops and POS devices in general, but virtually any place where you use a laptop, tablet or smartphone to enter personal data.
Long-time shoulder surfers did not usually loom behind their victims to scrutinize information. Instead, they stood at a safe distance and interpreted finger movements as people typed numbers on the keyboard . Similarly, today’s social engineers often escape attention as they quietly observe others in public places such as airport lounges and shopping malls, bars and restaurants, on trains or subways, or wherever there are people, to tell the truth.
Indeed, today’s most sophisticated criminals are watching from further away, hidden from view. They could use binoculars, micro cameras, or the camera of their phone or tablet to scan your screen or keyboard. Not only that, they may eavesdrop as you read credit card numbers on the phone or provide other sensitive information. Criminals could also take pictures, make a video or audio record of the information and then interpret it later.
Whatever the methodology, it is clear that technology has not only helped us to be more connected and be able to afford to pay for a frappuccino with our mobile phone, but it has also exposed us to security risks. When it comes to sensitive data, especially if there is a corporate account involved that could access other people’s sensitive data, you should never let your guard down , consequences could be very serious .
As shoulder surfing commonly happens
Before suggesting some methods to prevent shoulder surfing to be put into practice immediately, let’s take a closer look at how credential theft could happen with this technique.
At the bar or in the cafeteria
You’re in a busy restaurant bar waiting for a friend. To pass the time, you connect to Instagram. Unfortunately, you don’t notice that the person stuck in line next to you is looking at your password, which happens to be the same one you use for your email and bank account.
At the ATM
You’re taking cash at an ATM. You feel safe because the man after you in line is at least 10 feet away and is even looking at his phone. In fact, he is recording your finger movements on his phone and will later decrypt them to get your PIN number.
To the airport
Your flight is delayed, so grab your laptop and kill your time by reading a couple of work emails to keep up to date. Log in to the company website to read your mail and enter your username and password. You are so calm that you don’t see the woman a few places away as she stares at the screen while you enter data.

What are the consequences of shoulder surfing?
Using your credit card information to make fraudulent purchases is just one example of the damage you could suffer if you fall victim to shoulder surfing . The more personal information a criminal captures about you, the more serious the consequences can be for your bank account and financial health.
A serious case of shoulder surfing can expose you to identity theft . A criminal could use your personal information, such as your social security number, to open new bank accounts, apply for loans, rent apartments, or apply for a job under your name. An identity thief could get their hands on your tax refund, use your name to get medical treatment, or even apply for government benefits in your name. They could also commit a crime and provide your personal information when questioned by the police, leaving you with a dirty record or arrest warrant.
Of course, if you suspect this has happened, you’ll need to go to the police immediately, block your checking accounts and notify the bank. If fraudulent actions have already been carried out in your name, you may need to prove that you are not involved.
Things get dangerous if the stolen data is from a corporate account. In fact, with the use of valid credentials, anyone could enter the company’s system and perform all kinds of actions, such as collecting additional data, placing malware, running a ransomware , steal customer data and then sell it online.
How to defend yourself from shoulder surfing
Two levels of protection can be identified, the first is proactive and is aimed at preventing credentials from being exposed to malicious people, the second is active and provides software to detect attempts to use stolen credentials.

Defend yourself proactively
If you really can’t avoid entering sensitive data on your laptop, tablet or smartphone in a public place, you should follow the countermeasures listed below.
Tip 1: Before entering any sensitive data, find a safe place . Make sure you sit with your back to the wall. This is the best way to protect yourself from prying eyes. Avoid public transport, the central armchairs of a waiting room and places where there is a lot of people coming and going.
Tip 2: Use a privacy filter. This hardware device is a simple polarized translucent sheet that is placed over the screen. It will make your screen look black to anyone looking at it from any unnatural angle . This will make it much more difficult for unauthorized people to see your information.
Tip 3: Two-factor authentication requires a user to prove their identity using two different authentication components that are independent of each other. Since this type of authentication only passes when both factors are used correctly in combination, the security measure is particularly effective. For example, this method is often used a lot in online banking. There are many services that allow you to use your mobile phone as a second authentication factor . This is done through special apps.
Tip 4: Another solution is to use a password manager . By doing so, you no longer have to enter each password individually on your computer. The password manager will do this for you after you enter your master password . This prevents unauthorized people from using your keyboard to determine the real password, provided that you properly protect your master password .
Actively defend yourself with a SOC and behavior analysis
Now let’s imagine that the corporate account credentials have been stolen. At this point only a behavior control system can trigger an alarm and therefore block the user before there is any damage.
In fact, using correct credentials, a normal traditional SIEM would not trigger any alarms. For an older generation SIEM, access would be legitimate, because the credentials are correct. The attacker would have free undisturbed access to the system and could continue with his attack plan.
With SOD’s SOCaaS service, however, abnormal access would trigger an alarm. The SOC provided is equipped with a Next Generation SIEM and a system UEBA control behavior . This means that any deviation from the user’s usual behavior would be reported.
In the case of credential theft, as happens with shoulder surfing, the access made by the attacker would therefore trigger an alarm because something is wrong . For example, the login could take place at anomalous times, in another country / IP, from a different operating system, etc.
Conclusions
shoulder surfing is a social engineering technique that focuses on user carelessness while entering sensitive data into a system. In the event that a user’s corporate credentials are stolen, the only really efficient thing is to have a system that analyzes user behavior and reports whenever suspicious actions are detected.
If you want to know in detail how a SOC and UEBA system can help your company defend against social engineering attacks, do not hesitate to contact us, we will be happy to answer any questions.
Useful links:

Estimated reading time: 6 minutes
As the cybersecurity threat landscape becomes increasingly sophisticated, service providers, such as SOD, need to take additional precautions to protect their customers’ networks. An information management system and monitoring SIEM is an excellent choice in this respect.
This system, in fact, helps mitigate cybersecurity threats from two different angles, all from a single interface . The SIEM monitoring system collects information from multiple sources: network data, threat information feeds, compliance regulations, firewalls, etc. Next, uses that data to power features designed to help IT administrators respond to threat events in real time.

Advantages of SIEM monitoring
In contrast to individual security control systems such as asset management or network intrusion detection, SIEM allows you to dig deeper into security vulnerabilities by unifying information from various systems – even very and offering unprecedented visibility into events occurring in the system.
SIEM is not a threat detection system in and of itself, but enhances the security tools already in use by providing real-time insights to work from . In particular, SOD uses a Next Gen SIEM in a SOAR ( Security Orchestration, Automation and Response ) which also includes advanced behavioral analysis tools ( UEBA ).
If you put high-quality log files into a SIEM tool, you receive high-quality insights into network security . This information can help improve network security protocols.
Unfortunately, many administrators treat SIEM implementation as a solution to be set up and then forgotten. To experience the full benefits of managing information and security events , you need to implement a set of best practices to optimize your solution, starting with security logging.
The logs of a SIEM
How does security monitoring fit into SIEM implementation best practices ? If you look at the SIEM in its main components, it is a log management system .
All the information that a SIEM tool collects is in the form of logs, or records of events occurring within an organization’s IT infrastructure and network.
Examples of logs collected by SIEM include, but are not limited to: Firewalls, routers, wireless access points, vulnerability reports, partner information, antivirus and antimalware.
However, as SIEM tools have a very broad reach and constantly collect log data from all parts of the system, can be a bit complicated and impractical to implement . SIEM best practices help avoid pain points along the line of operation. This way you use SIEM as effectively as possible right from the start.

Best practice
1. Start calmly
The most common mistake made in implementing SIEM monitoring is trying to do too much too soon . Before you even start looking for a SIEM solution, in fact, it is best to define the scope of your SIEM implementation and think about what you want SIEM to do for your network and infrastructure.
We start by isolating the objectives , taking stock of existing security protocols and brainstorming how these protocols fit into the future SIEM implementation. You can also segment anything you want to monitor into groups and define how you want to monitor them. This helps ensure that you have a clear plan for logging.
Once an initial planning has taken place, the SIEM system does not yet have to be implemented across the entire IT infrastructure. It is better to proceed piecemeal.
You should then test the SIEM monitoring solution on a small section of the system to see how it works. Only then are key security vulnerabilities identified that should be addressed immediately and proceed with implementation in subsequent segments.
Setting up SIEM monitoring step by step, rather than running everything right away, will help ensure that logging works in harmony with the rest of the IT section .
2. Think about the requirements
SIEM monitoring can help the company demonstrate compliance with security regulations and audits, but only by knowing what these standards are in advance . Before committing to a SIEM system, you create a list of HIPAA, GDPR, HITECH and any other IT regulations that you need to comply with. The list is then used to compare the required regulations with the solutions that are put into practice.
Not only does this narrow down the list of standards, it will force you to consider how much log data you actually need. Keeping the correct amount to be compliant, also aligns with best practices of SIEM logging and monitoring .
Obviously, the solutions and protocols to follow are not the same for everyone and need to be adapted according to the position of the individual company. For this particular aspect, SOD can help your company both in gathering the information necessary to identify which standards to follow, and in the standards verification once implemented.
3. Fix the correlations
SIEM correlation streamlines its implementation, allowing you to configure the system according to the specific needs of their customers. SIEM works by collecting data from multiple sources and then filtering, analyzing and correlating it to determine if it deserves to be reported as a security alert.
For this it is essential to correlate the rules and set alarm thresholds based on the type of data and their origin . It is important to remember, in fact, that SIEM is designed to find connections between events that would not otherwise be related to each other.
Setting up a SIEM monitoring system is a delicate but fundamental operation to improve the security system for a particular company.
4. Collect data efficiently
Through a SIEM monitoring system it is possible to collect such an amount of data that it could become complicated to manage. It becomes important to choose in a balanced way which data to use in order to optimize the right amount without losing the advantage of having the entire system under control .
Among the data that it is better not to leave out are: Successful permissions and failed attempts, changes to user privileges, application errors and performance problems, opt-in and in general all the actions made by users with administrative privileges.
The following are excluded: information whose collection is illegal, banking information or credit card data, encryption keys, passwords and personal data .
5. Have a plan in case of a detected threat
Choosing the right SIEM solution and employing logging best practices is only part of the job. You need to have an action plan in case of cyber threat .
For the company that relies on a MSSP as SOD, this means making sure that monitoring is only the first part of the service provided. Ideally, SIEM monitoring is the first piece of a well-designed SOAR that puts in place professional operators, alert notifications and a recovery plan in accordance with the type of data put at risk .
In this respect, the SOC as a Service we offer covers most of the eventualities.

Conclusions
Monitoring is a fundamental part of the corporate security system and a SIEM is one of the ways to put it into practice. However, we must not stop at the collection of information, we must know how to treat, enrich and analyze it.
SOD offers comprehensive services that implement SIEM monitoring systems. The implementation obviously implies a “calibration” of the systems and of the correlations between the data in order to always offer the most suitable solution.
If you would like more information about our products, do not hesitate to contact us, we will be happy to answer your questions.
Useful links:
Useful links:
Next Generation SIEM: where are we?

Customers
Twitter FEED
Recent activity
-
SecureOnlineDesktop
Estimated reading time: 6 minutes L'impatto crescente delle minacce informatiche, su sistemi operativi privati op… https://t.co/FimxTS4o9G
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The growing impact of cyber threats, on private or corporate operating systems… https://t.co/y6G6RYA9n1
-
SecureOnlineDesktop
Tempo di lettura stimato: 6 minuti Today we are talking about the CTI update of our services. Data security is… https://t.co/YAZkn7iFqa
-
SecureOnlineDesktop
Estimated reading time: 6 minutes Il tema della sicurezza delle informazioni è di grande attualità in questo peri… https://t.co/tfve5Kzr09
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The issue of information security is very topical in this historical period ch… https://t.co/TP8gvdRcrF
Newsletter
{subscription_form_1}© 2023 Secure Online Desktop s.r.l. All Rights Reserved. Registered Office: via dell'Annunciata 27 – 20121 Milan (MI), Operational Office: via statuto 3 - 42121 Reggio Emilia (RE) – PEC [email protected] Tax code and VAT number 07485920966 – R.E.A. MI-1962358 Privacy Policy - ISO Certifications













