Estimated reading time: 9 minutes
Spam seems to reach every single email account we use , no matter how careful we are or what the address provider is. How do spammers get all of our email addresses? Can we do something to hide our email address from common spammer techniques?
Unfortunately, there’s not much you can do to stop spammers from bombarding you with emails. There are some tips that will help protect you, but spammers will probably find your email address anyway .
The problem is not so much the unwanted advertisement message, but rather what it means that you received a message. How did you react? Did you delete it? Did you click on any links? Have you flagged it as spam? Any action could bring useful information to attackers without you noticing.
Let’s face it more clearly and start with a question: where do spammers find our e-mails?
Spammer techniques for retrieving e-mail addresses
Nobody gives their email to a website and expects it to end up in the hands of a scammer. Yet it’s not uncommon for someone to find their inbox full of unsolicited spam emails.
Stolen databases
The simplest of the techniques spammers use to collect large lists of active email addresses is through stolen account databases. These password thefts happen with frightening regularity. Companies like Adobe, LinkedIn, eHarmony, Gawker, Last.fm, Yahoo !, Snapchat and Sony have all been compromised in recent years .
Leaked databases are normally considered a security threat because they often display account names and passwords. However, generally show email addresses as well. Spammers can download these leaked databases and add the millions of email addresses to their lists . Spammers know that most of these email addresses should be active , so these databases are excellent for them.
This is probably how most spammers are finding email addresses to send spam. There really isn’t much you can do to protect yourself from a spammer who gets your address this way.
A site like Have I been pwned? can tell you if the information of your account may have been spread .
You can protect yourself from password theft by using different ones, unfortunately, you must always use the same email address everywhere , it would be unthinkable to have an address for each service used.
Link in mail messages
If you receive spam emails, you should avoid clicking on the links in the email . If you find an “Unsubscribe” link in an email from a legitimate company, it’s probably safe to click it. A real company doesn’t want to spam and potentially run into anti-spam laws, so they will simply remove you from their list.
However, if you see an “Unsubscribe” link (or, even worse, a “Buy Now!” link) in an email that looks very unprofessional and scam, the spammer will not necessarily remove you from his lists .
This is where things get more complex. They will notice your click and their systems will identify your email address as active . They know you’re there, and you may see larger amounts of spam after clicking the link.
The same goes for uploading images in spam emails. Do not click the “Upload images” button, or spammers will know that you have opened the email . Even if you don’t see an image in the message, there may be a small tracking pixel that allows the spammer to identify you if you upload the asset.
This is why most email clients don’t automatically upload images.

E-mail scraping, search for unencrypted e-mails on the net
Another spammer technique to retrieve addresses from the network is to scrape them ( scraping ) from the unencrypted data on the network. There are software out there that read files on the net and find those that contain e-mails and save them. A bit like Google’s crawlers do when they crawl a site, but with malicious intent.
You may have seen a comment where someone leaves their address to be contacted. The bot that scans the network will save similar addresses.
The spammer adds this address to his spam lists et voilà , spam is served . This is why eBay provides a temporary email address where you can be reached rather than including your real email address. This technique is probably less common now that spammers have huge leaked account databases to work with.
Spammers can also try to acquire valid email addresses by browsing other places that are publicly available, such as whois records for a domain . These records show an email address associated with the person or organization that registered the domain name.

Purchase of email addresses
Another spammer technique, definitely for lazy hackers, is to buy addresses from databases that provide them.
Unscrupulous people sell email lists to spammers for a low price. These addresses were often distributed on CD in the past , and may still be, but the leaked account databases have probably eliminated some interest in this market.
Spammers can also simply exchange their mailing lists with each other, making sure other bad guys get their hands on your address once it happens the first time.
Please be aware that this technique is not entirely illegal. When we subscribe to a service, we often have the possibility to provide our e-mail address to third parties for advertising purposes. Some users accept without reflection and without verifying whether it is an obligation to subscribe to the service or not. .
I personally happened to be contacted by a person who, with no intent to spam, but to make up the number, had bought my address from a contact resale agency, divided by areas of interest. If he had been a spammer, he could have used a similar service.
How to protect your address
Spammers can also obtain email addresses in other ways but the methods listed above are some of the most common.
There isn’t much you can do to prevent your email address from being leaked and receiving spam.
- – you can avoid putting your e-mail address on the web in plain text form
- – never click on a link
- – don’t upload a image in a suspicious email.
However, your address will almost certainly end up in the hands of a spammer at some point.
Actually, you don’t have to worry so much about whether the address is in circulation, but about how the address is used, especially if it is active.
Spammer techniques of using addresses
Once a scammer obtains your email address, it is very likely that they will use it to take advantage in any way possible . The better he is, the greater the risks.
Many will send you spam emails, with the hope of collecting private information such as credit card numbers . They will try to trick you into believing that you have won something, or that they have a profitable item for sale. Hackers may also use your email to steal your identity and send messages to your contacts . Remember the techniques of Zombie Phishing ?
Other scammers will use your personal information to try to access your other accounts . Most people reuse the same passwords for different accounts, which means that hackers who have access to one account can easily infiltrate the others.
This is why using the same passwords around the web is highly discouraged and not secure at all.
Create botnets
One of the reasons why you should never actively interact with spam messages is that interactions send hackers an important piece of information: the address is active, someone uses it on their device.
An active address, once discovered, is a perfect target for more specific attacks than phishing , and since all addresses are at risk, even corporate ones, from phishing you can easily get to a double extortion ransomware .
In the latter case, the threat of a DDoS attack may already come from mentioned zombie phishing technique, and it could all have started with some spam message.
The computers that will basically send requests to the server to perform the DDoS attack could themselves be part of a botnet created as a result of techniques used by spammers .

Phenomenology of an attack
As a first spammer technique, company addresses are retrieved . This can be done through scraping or database buying on the dark web. Next, to check which addresses are active , a couple of spam campaigns are sent. Nothing harmful, fake newsletters with an obvious Unsubscribe message, or a tracking pixel.
Note: A tracking pixel is usually a very small transparent image that is uploaded from a remote server. Just check how many times it has been downloaded and by whom to understand which addresses are active and which are not .
As a result, the contact database will have shrunk to a list of active addresses , in which users have been inattentive enough to click on a link from a suspicious email.
Finally, to these selected addresses, is sent a real phishing message containing malware or a request to intervene on a seemingly legitimate web page . For example, the request to reset your credentials via the attached link.
The unsuspecting user, thinking he is doing a safe thing, follows the link, enters the credentials and gives them to the spammer . At this point the attacker has gained access to an account. From that moment on, the risks are much more and much more damaging.
How to defend against spammer techniques
Let’s take a few steps back. The whole chain of events that led the hacker to gain access to an important account went through spam and phishing messages.
Ethical Phishing
In some of the passages, the attack could have been avoided . The ability to recognize a suspicious message and then ignore it is the first weapon available to a user. SOD can help your business with this .
Through a ethical phishing service, we first test the resilience of users . Once any weak points have been identified, a training course ad hoc is constructed to provide adequate proactive defense tools to all employees.
SOC as a Service
Not always being aware users is enough , and a careless mistake could cost a company a lot of sensitive data. For this reason, we can also implement a service SOCaaS for the mitigation of risk and damage following an attack.
In this scenario, a system consisting of next generation SIEM and protocols UEBA implemented by an artificial intelligence, they monitor the network in search of any anomaly . Any suspicious behavior is identified and analyzed by technicians to see if it can actually become a threat or not.
If you would like more information on how SOD can help you raise your company’s cybersecurity level, don’t hesitate to contact us.
Useful links:

Estimated reading time: 6 minutes
Out of nowhere, someone replies to an email conversation dated months ago. This is a real conversation that actually happened. Maybe it’s about a meeting, a job opportunity. This email seems very relevant, but beware, it could be zombie phishing .
Indeed, something is wrong, the topic discussed has been over for months and now there is a strange error message in the body of the email. This is a sneaky tactic: revive a long dead email conversation.

Not the usual phishing
The Cofense ™ Phishing Defense Center ™ (PDC) spotted a large Zombie Phishing campaign in 2018. The scam , like almost any phishing attack, is carried out through compromised email accounts.
Scammers take over an email account and respond to long-closed conversations with a phishing link or malicious attachment (e.g. malware or a keylogger ) . Since the email subject is usually relevant to the victim, a curiosity-driven click is very likely to occur . In fact, let’s not forget that the original conversation was already present in the messages received, it is easy to think that it is a follow up or similar.
These Zombie Phishing attacks appear to use automatically generated infection URLs to evade detection. No two links are alike, and they are hidden behind “error” messages without too many frills in the body of the message. This scenario provides a pattern of apparent legitimacy for the users who are victims.
The zombies in computer science
In the computer industry, a zombie is a compromised computer connected to the network. The compromised state could be due to a hacker, virus, malware, or trojan horse .
The infected machine performs malicious tasks under a remote direction. Zombie computer botnets are often used to spread email spam and launch denial-of-service (DoS) attacks.
Types of attack
Here are some observed patterns of Zombie Phishing carrying malicious links . A distinguishing factor was the use of two distinct graphic templates containing button or link error messages.
The message reads something like “Incomplete message” or “Inability to show the whole message”. The link or button invites you to click to see the original message. Obviously the click only involves the installation of a malware or other similar events . Note that no two identical links have been identified, a sign that probably a bot was generating the addresses.
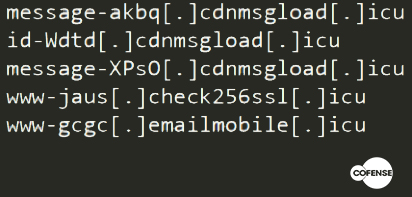
Another common factor is the use of domains with the .icu TLD. This is probably a factor that varies considerably over time. Here are some of the domains found in the first analysis of 2018:
These zombie phish attacks have been observed to use official organizational logos to add legitimacy to the fake login pages. A common practice in phishing techniques that we have already seen in other articles.
Landing pages are designed to look like a legitimate online portal, including a company logo and even a favicon. In these cases the ultimate goal is the theft of the victim’s credentials .
Furthermore, any victim who visits the malicious website is “tagged” using the host’s IP address as an identifier and, after entering the credentials, is directed to the same spam website seen by other victims. This is often done via obfuscated links using URL shorteners (such as hxxps://href[.]Li/).
If the same host tries to visit the phishing link again, the fake login page is skipped and you are forwarded directly to the spam page. This markup and URL shortener obfuscation helps attackers keep a low profile and continue their campaign unabated.
Conversation Hijacking

The conversation hijacking tactic is by no means new and is now living a new life with zombie phishing . Scammers have hijacked compromised email accounts to distribute malware and phishing emails as replies to conversations that have been concluded for years now.
This technique is still popular because it makes victims much more likely to click on links and download or open files. The threshold of attention against classic phishing attacks is lowered when messages are brought into conversations already in their inbox .
A couple of years old example of this was the botnet Geodo . Basically it is insertion into existing email threads ( conversation hijacking ) to deliver malicious documents. These, in turn, download a sample of Geodo or other malware such as Ursnif , which according to Key4Biz was the most widespread in Italy in June 2020.
However, the effectiveness of this tactic can greatly depend on the content of the conversations . A reply to an automated advertising email is less likely to cause an infection than a reply to a help-desk support thread.
There have been several Geodo zombie phishing campaigns consisting of replies to automated advertising emails. This is an indication that, in some cases, campaigns consist of indiscriminate replies to all emails in a mailbox. Since the volume of these conversation hijacking is still relatively low, the small reach of these emails is probably limited by the number of ongoing conversations .
Certain account types are therefore more likely to attract the direct attention of threat actors and induce them to invest additional effort and time in developing unique phishing campaigns for those accounts.
Defense from zombie-phishing
Here are some quick tips to avoid losing your credentials in a Zombie Phishing attack:
- Beware of email subjects that may seem relevant but come from old conversations
- Beware of any error message in the body of the message
- Don’t trust attached documents just because they’re replying to a conversation
- Hover your mouse over buttons or links in suspicious messages to check for suspicious domains
It has been observed that these campaigns have gotten smarter . To combat this and other forms of phishing, employee training is key.
A properly trained workforce is what it takes to defend your organization against Zombie Phishing attacks.
SOD offers a full service in this regard . We begin by attacking the company in a controlled manner, testing any weaknesses in employee safety or behavior. Subsequently, specific training is designed to remedy the gaps and fully train the staff.
To keep defenses high, our SOCaaS includes the analysis of user behavior, logs of connected machines and the network in a to immediately identify phishing attempts.
Useful links:
Customers
Twitter FEED
Recent activity
-
SecureOnlineDesktop
Estimated reading time: 6 minutes L'impatto crescente delle minacce informatiche, su sistemi operativi privati op… https://t.co/FimxTS4o9G
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The growing impact of cyber threats, on private or corporate operating systems… https://t.co/y6G6RYA9n1
-
SecureOnlineDesktop
Tempo di lettura stimato: 6 minuti Today we are talking about the CTI update of our services. Data security is… https://t.co/YAZkn7iFqa
-
SecureOnlineDesktop
Estimated reading time: 6 minutes Il tema della sicurezza delle informazioni è di grande attualità in questo peri… https://t.co/tfve5Kzr09
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The issue of information security is very topical in this historical period ch… https://t.co/TP8gvdRcrF
Newsletter
{subscription_form_1}© 2023 Secure Online Desktop s.r.l. All Rights Reserved. Registered Office: via dell'Annunciata 27 – 20121 Milan (MI), Operational Office: via statuto 3 - 42121 Reggio Emilia (RE) – PEC [email protected] Tax code and VAT number 07485920966 – R.E.A. MI-1962358 Privacy Policy - ISO Certifications