LOG AGGREGATOR
FLEXIBLE, LOW-FOOTPRINT LOG COLLECTION SERVICE WITH SOFTWARE AGENTS FOR 50+ PLATFORMS Log Management service comes with the possibility of using syslog-ng Premium Edition as log collection agents or relay servers at no additional cost. Installers are available for 50+ platforms, including the most popular Linux distributions, commercial flavors of UNIX and Windows. Become a ResellerHIGHLY SCALABLE INDEXING ENGINE
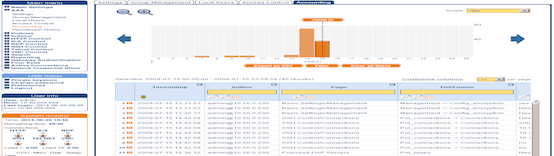
The Log Management service is optimized for performance, and can handle enormous amounts of messages. Depending on its exact configuration, it can index over 100,000 messages per second for sustained periods and process over 70 GB of raw logs per hour.
REAL-TIME LOG DATA TRANSFORMATION
Filter, Parse, Re-Write
The syslog-ng application can sort the incoming log messages based on their content and various parameters like the source host, application, and priority. Directories, files, and database tables can be created dynamically using macros. Complex filtering using regular expressions and boolean operators offers almost unlimited flexibility to forward only the important log messages to the selected destinations
Parse key-value pairs
Log Aggregator can separate a message consisting of whitespace or comma-separated key-value pairs (for example firewall logs) into name-value pairs.
Parse sudo log messages
Privileged user accounts represent the highest security risk, as they allow access to the most sensitive data and resources. The sudo parser enables you to enrich your log message data with details of privilege escalation events.
Normalize data with PatternDB
The syslog-ng application can compare the contents of the log messages to a database of predefined message patterns.
Real-time log message classification
By comparing log messages to known patterns, syslog-ng is able to identify the exact type of the messages, and sort them into message classes. The message classes can be used to classify the type of the event described in the log message. The message classes can be customized, and, for example, can label the messages as user login, application crash, file transfer, etc.
Extracting important information from messages
In addition to classifying messages, you can also add different tags which can be used later for filtering messages, for example, to collect messages tagged as user_login to a separate file or to perform conditional post processing on the tagged messages.
Real-time event correlation
Syslog-ng also makes real-time event correlation possible. This can be useful in many different situations. For example, important data for a single event is often scattered into multiple syslog messages. Also, login and logout events are often logged far away from each other, even in different log files, making log analysis difficult. Using correlation these can be collected into a single new message.
AUTOMATED BACKUP OF STORED DATA
Stored log messages and the configuration of SSB can be periodically transferred to a remote server using the following protocols
:
- Network File System protocol (NFS);
- Rsync over SSH;
- Server Message Block protocol (SMB/CIFS).
Customers
Twitter FEED
Recent activity
-
SecureOnlineDesktop
Estimated reading time: 6 minutes L'impatto crescente delle minacce informatiche, su sistemi operativi privati op… https://t.co/FimxTS4o9G
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The growing impact of cyber threats, on private or corporate operating systems… https://t.co/y6G6RYA9n1
-
SecureOnlineDesktop
Tempo di lettura stimato: 6 minuti Today we are talking about the CTI update of our services. Data security is… https://t.co/YAZkn7iFqa
-
SecureOnlineDesktop
Estimated reading time: 6 minutes Il tema della sicurezza delle informazioni è di grande attualità in questo peri… https://t.co/tfve5Kzr09
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The issue of information security is very topical in this historical period ch… https://t.co/TP8gvdRcrF
Newsletter
{subscription_form_1}© 2023 Secure Online Desktop s.r.l. All Rights Reserved. Registered Office: via dell'Annunciata 27 – 20121 Milan (MI), Operational Office: via statuto 3 - 42121 Reggio Emilia (RE) – PEC [email protected] Tax code and VAT number 07485920966 – R.E.A. MI-1962358 Privacy Policy - ISO Certifications