Web Hosting
 Giacomo Lanzi
Giacomo Lanzi
HTTP / 3, everything you need to know about the latest version protocol
Security researchers have just digested the HTTP / 2 protocol, but web innovators are already publishing an update: HTTP / 3. This technology offers performance gains and security benefits, but only if we overcome the implementation problems that await us for what appears to be an evolutionary change rather than a real revolution in the way the web works. In…
 Giacomo Lanzi
Giacomo Lanzi
The threat of DDoS ransomware
Is the threat of a large-scale DDoS attack enough to convince organizations to bow to a ransomware attack? It might be a good time for companies to invest in DDoS protection , as hackers have begun to use the threat of large-scale DDoS attacks to carry out ransomware attacks on organizations . According to a new blog post from Cloudflare,…
 Giacomo Lanzi
Giacomo Lanzi
Protecting a site in WordPress: security package
Whether it’s WordPress or not, your website is potentially vulnerable to attack. Recent reports have shown that Google blacklists thousands of websites containing malware and phishing attacks every week. Considering how serious the potential security breaches can be for your business, we hope this article informs you why you should always protect your WordPress site. Is protecting a WordPress site…
 Giacomo Lanzi
Giacomo Lanzi
Plesk panel: available applications
On the web there are many open source applications that allow you to manage the most various situations. It is common practice for these applications to be available for installation from your hosting control panel. The Plesk panel makes no exceptions. So let’s see what are the main applications available for installation. How to install applications from the Plesk panel…
 Giacomo Lanzi
Giacomo Lanzi
PageSpeed Insight: better speed with Google
If the site is slow, you are losing customers. It’s very simple and there are no kinder ways to say the same thing. The speed of a site is directly proportional to the desire of a user to visit it. To measure your portal you can use a tool made available by Google: PageSpeed Insight. You can access this service…
 Giacomo Lanzi
Giacomo Lanzi
Node.js via SOD hosting panel
If you are interested in hosting Node.js apps on your web space, we have good news! The control panel offered by SOD, based on Plesk, is equipped with a Node.js extension that allows you to easily manage applications. In this article we see how it is possible to integrate Node through the control panel. Host a Node.js application from the…
 Giacomo Lanzi
Giacomo Lanzi
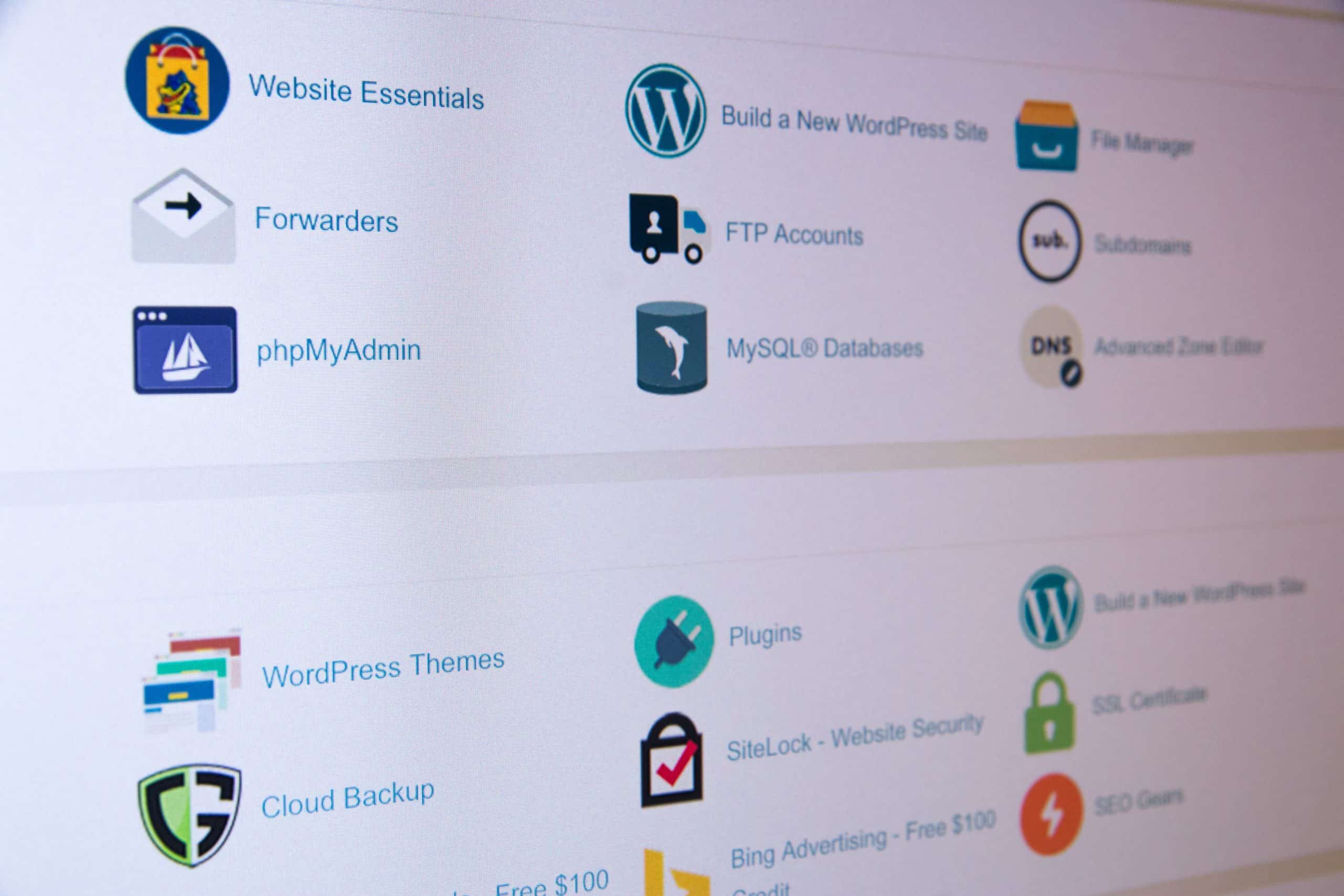
cPanel and Plesk the best for hosting management
Most hosting environments use an intuitive interface to help users manage their web spaces. Two very famous panels are cPanel and Plesk, widely used and offered in the SaaS formula. Without these graphical interfaces, it would be difficult to manage a hosting space and set up a site. A lot of time is usually spent managing a web space through…
 Giacomo Lanzi
Giacomo Lanzi
Updating php: why and how
PHP is one of the most popular scripting languages on the web today. According to W3Techs, PHP is used by over 82% of all websites that use a server-side programming language. This means that 8 out of 10 sites use PHP in one form or another. Being a scripting language, it is essential to update PHP to the latest version…
 Giacomo Lanzi
Giacomo Lanzi
Manage WordPress from the hosting panel
With Secure Online Desktop hosting plans, you have access to a convenient control panel. In addition to the collection of all information on the status of the server, the management of mailboxes and files, it is also possible to access a dedicated panel to manage WordPress in all its aspects. The section of the panel is called WordPress Toolkit and…
 Giacomo Lanzi
Giacomo Lanzi
Server hosting for SOD website
Based on what the actual need is, choosing hosting for a website is essential. The resources needed to host a fast and secure portal must be the basis on which to decide which plan to choose. Choosing the right provider for the server hosting plan can be complicated, and it’s easy to get lost in the alternatives that the network…
 Giacomo Lanzi
Giacomo Lanzi
Online hosting for websites
Online hosting is the process of using space on a remote server to host a website. The content of the pages (HTML, CSS, images, etc.) must be loaded into the server space to be reached online. Website hosting service providers have servers, connectivity and associated services for hosting online pages. By offering a variety of plans for online hosting, they…
 Piergiorgio Venuti
Piergiorgio Venuti
CloudFlare free Plesk extension for Webhosting users
ClouCloudFlare protects your websites from online threats and DDoS attacks, while making them twice as fast around the world. CloudFlare runs a globally distributed network. Once you enable CloudFlare on your website via Plesk Admin Panel, the traffic routes through the CloudFlare network before it reaches your server. CloudFlare stops malicious web traffic, fights DDoS attacks and automatically caches and…
 Piergiorgio Venuti
Piergiorgio Venuti
Let’s Encrypt Free Certificates for all Webhosting users
Let’s Encrypt is a free, automated and open Certification Authority. The objective of Let’s Encrypt and the ACME protocol is to make it possible to set up an HTTPS server and have it automatically obtain a browser-trusted certificate, without any human intervention. This is accomplished by running a certificate management agent on the web server. With our Webhosting service based on Plesk technology you…
 Alessandro Stesi
Alessandro Stesi
WEB HOSTING
Now available the new WEB HOSTING service and domain registrations by Secure Online Desktop. The web hosting service with the 3 packages Starter, Business and Ultimate enable you to create professional websites, get Databases and create e-mail accounts, starting from € 29.99. For the most demanding companies are always at your disposal VPS services and Cloud Server solutions. Learn more……
Customers
Twitter FEED
Recent activity
-
SecureOnlineDesktop
Estimated reading time: 6 minutes L'impatto crescente delle minacce informatiche, su sistemi operativi privati op… https://t.co/FimxTS4o9G
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The growing impact of cyber threats, on private or corporate operating systems… https://t.co/y6G6RYA9n1
-
SecureOnlineDesktop
Tempo di lettura stimato: 6 minuti Today we are talking about the CTI update of our services. Data security is… https://t.co/YAZkn7iFqa
-
SecureOnlineDesktop
Estimated reading time: 6 minutes Il tema della sicurezza delle informazioni è di grande attualità in questo peri… https://t.co/tfve5Kzr09
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The issue of information security is very topical in this historical period ch… https://t.co/TP8gvdRcrF
Newsletter
{subscription_form_1}© 2023 Secure Online Desktop s.r.l. All Rights Reserved. Registered Office: via dell'Annunciata 27 – 20121 Milan (MI), Operational Office: via statuto 3 - 42121 Reggio Emilia (RE) – PEC [email protected] Tax code and VAT number 07485920966 – R.E.A. MI-1962358 Privacy Policy - ISO Certifications












