ICT Monitoring
 Giacomo Lanzi
Giacomo Lanzi
Monitoring system, an overview
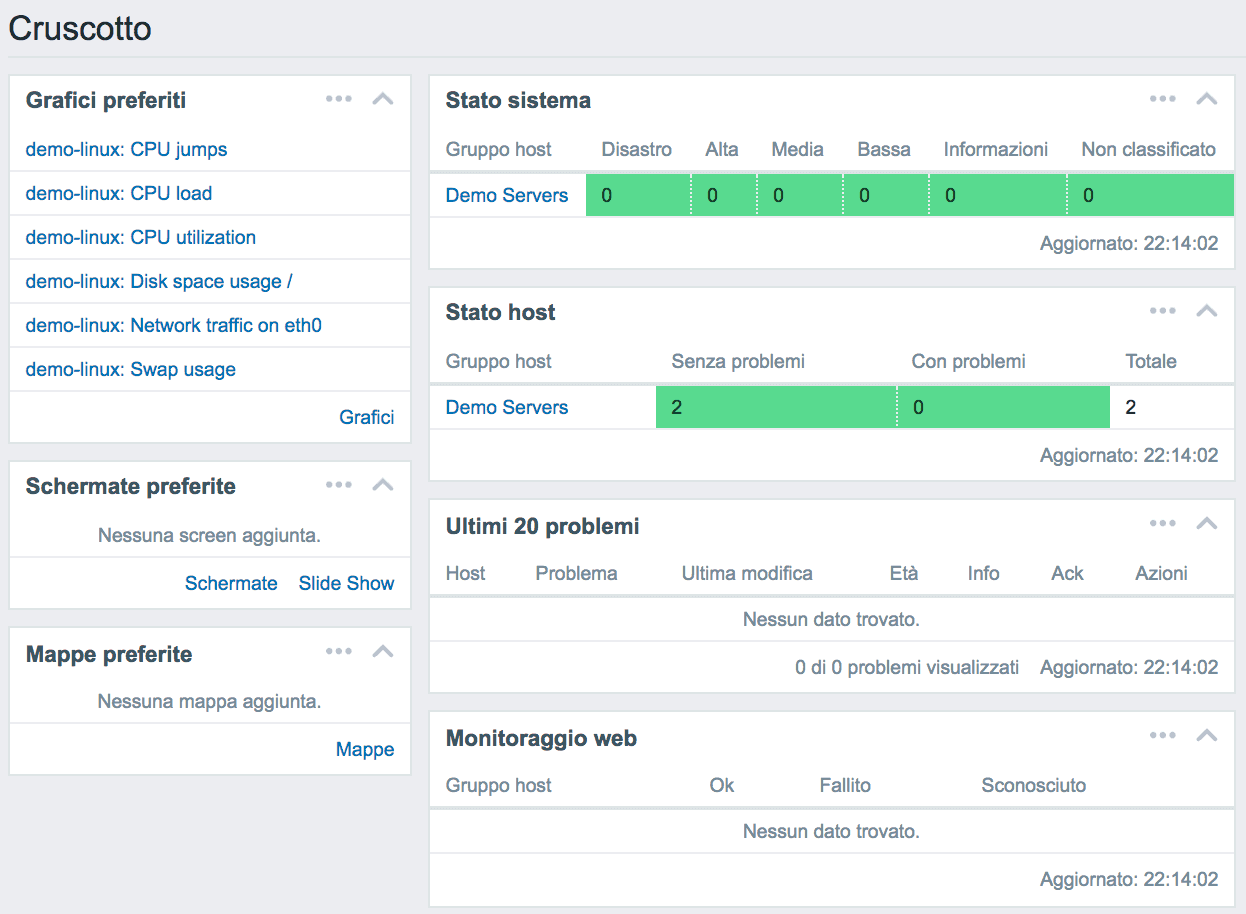
Zabbix is a monitoring system suitable for different IT components, including networks, servers, virtual machines (VMs) and cloud services. Zabbix provides metrics such as network usage, CPU load, and disk space consumption. The software monitors operations on Linux, Hewlett Packard Unix (HP-UX), Mac OS X, Solaris, and other operating systems (OS);however, Windows monitoring is only possible through specific agents. SOD…
 Giacomo Lanzi
Giacomo Lanzi
Zabbix: Web console for monitoring
An indispensable tool for keeping complex infrastructure controlled is a monitoring system. Secure Online Desktop (SOD) Web Console does just that: it offers the tools to control a network of machines and devices to verify its efficiency. Web Console is based on Zabbix, a scalable Open Source platform with huge capabilities. Among the advantages of the SOD Web Console, there…
 Giacomo Lanzi
Giacomo Lanzi
IT monitoring system – Operation
Once you set up an IT development and management environment, it can be difficult to keep everything under control. IT monitoring systems come in handy, specifically designed to keep the entire system monitored. The monitoring system of an ICT infrastructure allows you to report any anomalies that may occur within the components of the IT network. In this world, it…
 Alessandro Stesi
Alessandro Stesi
How to have your computer network under control
monitoring In recent years we have witnessed a rapid evolution of information infrastructures that have become increasingly complex and heterogeneous. The introduction of virtualization, thanks to the economic savings and its simplicity, has encouraged the increase in the number of servers divided then by functions and roles. Technologies like the Cloud have allowed to extend the company boundaries, just think…
Customers
Twitter FEED
Recent activity
-
SecureOnlineDesktop
Estimated reading time: 6 minutes L'impatto crescente delle minacce informatiche, su sistemi operativi privati op… https://t.co/FimxTS4o9G
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The growing impact of cyber threats, on private or corporate operating systems… https://t.co/y6G6RYA9n1
-
SecureOnlineDesktop
Tempo di lettura stimato: 6 minuti Today we are talking about the CTI update of our services. Data security is… https://t.co/YAZkn7iFqa
-
SecureOnlineDesktop
Estimated reading time: 6 minutes Il tema della sicurezza delle informazioni è di grande attualità in questo peri… https://t.co/tfve5Kzr09
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The issue of information security is very topical in this historical period ch… https://t.co/TP8gvdRcrF
Newsletter
{subscription_form_1}© 2023 Secure Online Desktop s.r.l. All Rights Reserved. Registered Office: via dell'Annunciata 27 – 20121 Milan (MI), Operational Office: via statuto 3 - 42121 Reggio Emilia (RE) – PEC [email protected] Tax code and VAT number 07485920966 – R.E.A. MI-1962358 Privacy Policy - ISO Certifications












