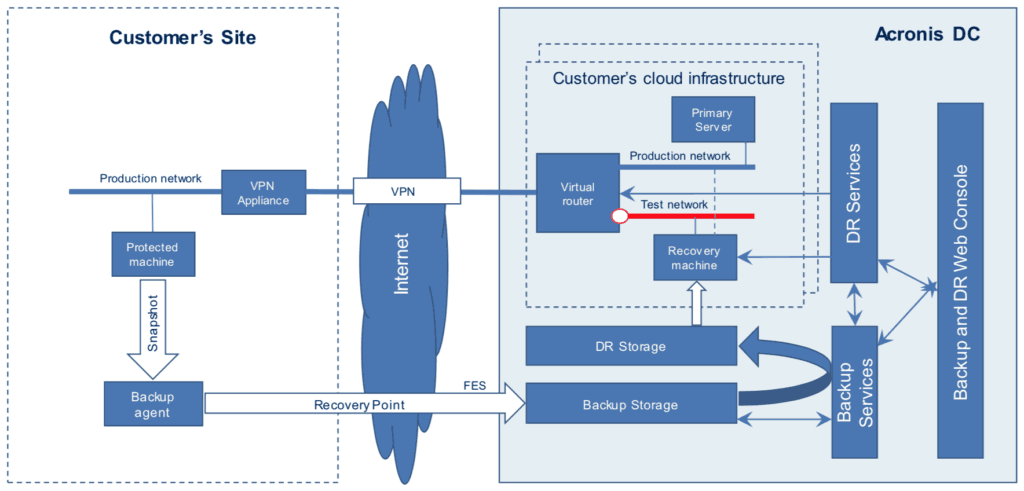
The Architecture Overview
Extension of Local Networks to Acronis Cloud Recovery Site
♦ A local network and Acronis Cloud Recovery Site are connected over a fast and secure VPN tunnel.
♦ Network parameters auto discovery.
♦ Customer’s network is “stretched” tothe cloud with transparent access to cloud servers like they are on the local network.
♦ The VPN tunnel is not used for replication.
♦ Users outside the production network can access the cloud recovery site directly via VPN client software.
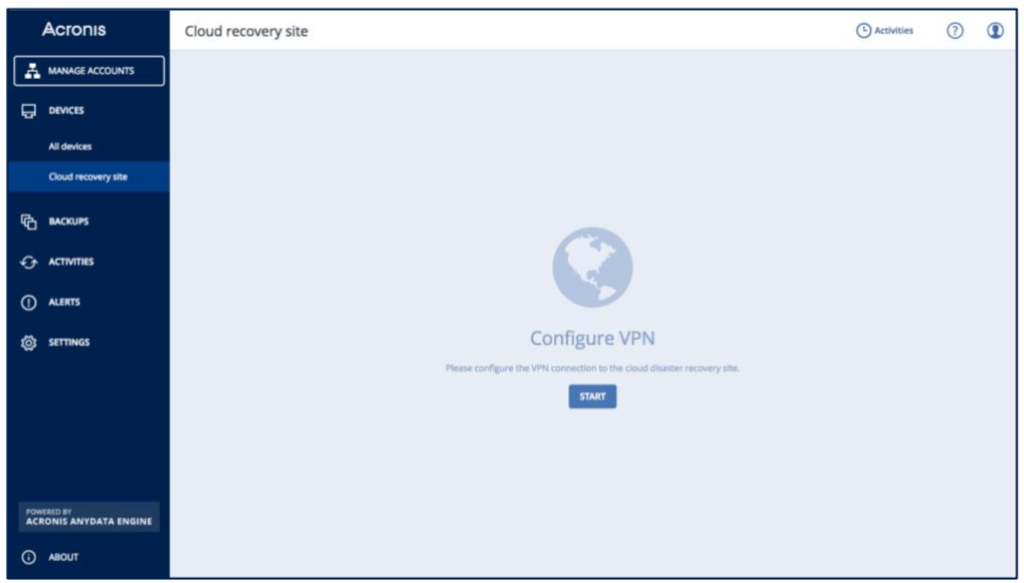
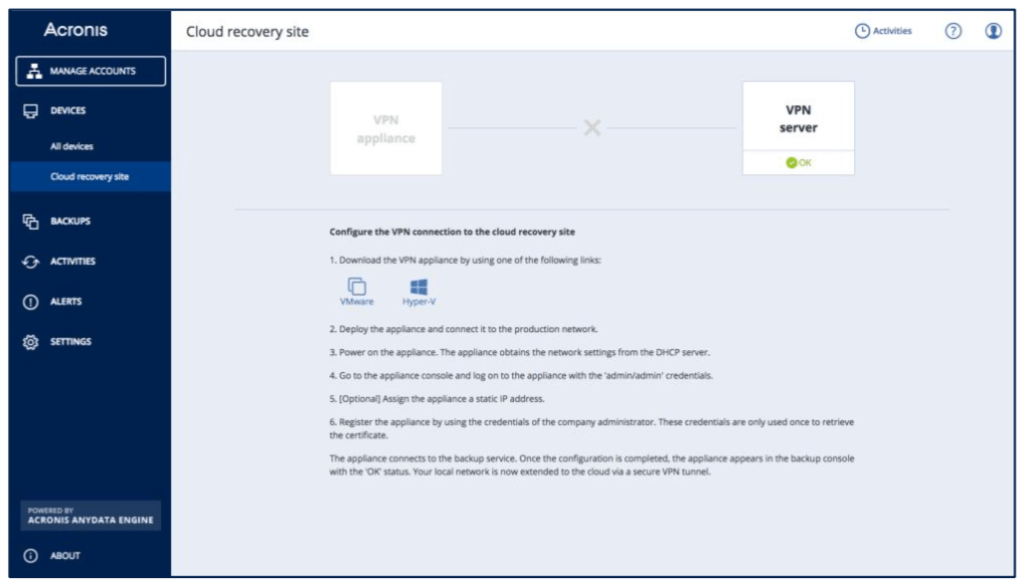
Establishing a VPN Connection
♦ A simple and automated VPN connection configuration takes minutes and only needs to be done once
♦ The VPN server is automatically deployed in the Acronis Cloud
♦ An administrator downloads and deploys a small virtual appliance to extend the production network into the cloud
♦ ESXi or Hyper-V templates are available for the VPN appliance
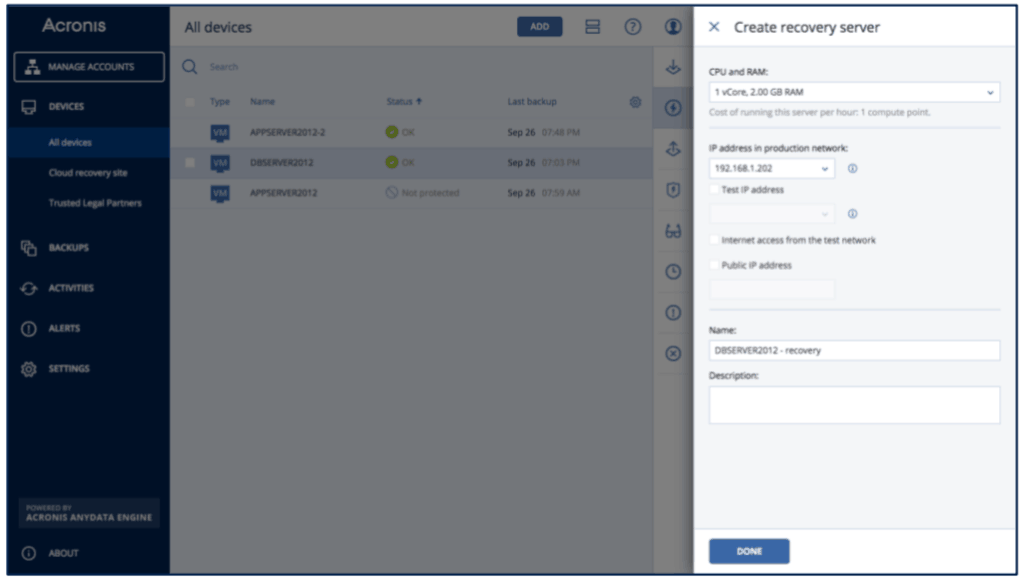
Protecting a Machine with Recovery Server
♦ The recovery server is a replica of a protected server, which spins up in an Acronis Data Center and is used for fail over or a failover-readiness check
♦ Easily sets up in seconds
♦ Uses Acronis Backup Cloud recovery points to start a machine
♦ CPU and RAM can be adjusted
♦ An optional public IP address can be purchased
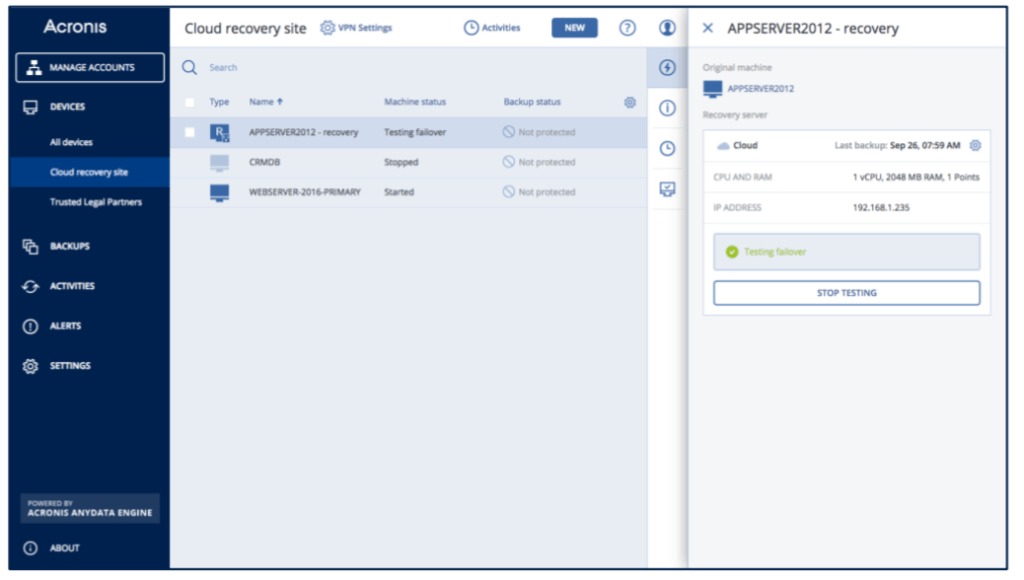
Testing a Failover
♦ As a part of regular disaster readiness checks, any protected server can be started in an isolated network in a non-disruptive manner
♦ Most popular remote access protocols are supported (SSH and RDP)
♦ Optional internet access is available through NAT and external IP address
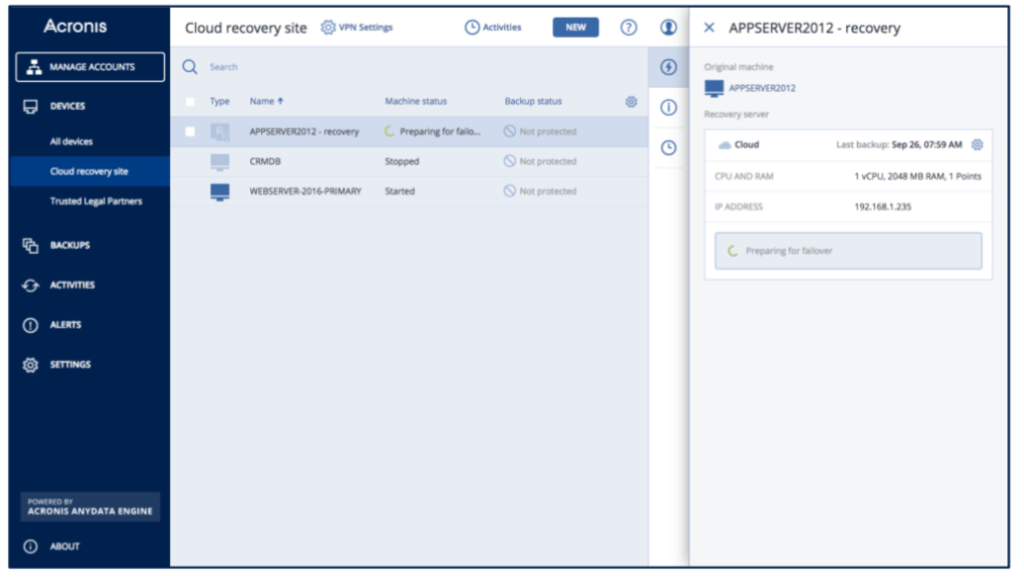
Performing a Failover
♦ Production failover is executed in case of original failure
♦ The recovery server is started in minutes and is moved to shared, high-performance storage
♦ The recovery server in a failover mode is fully accessible through site-to-site VPN, point-to-site VPN, and optionally, the public network
♦ Any available recovery point can be used for a failover
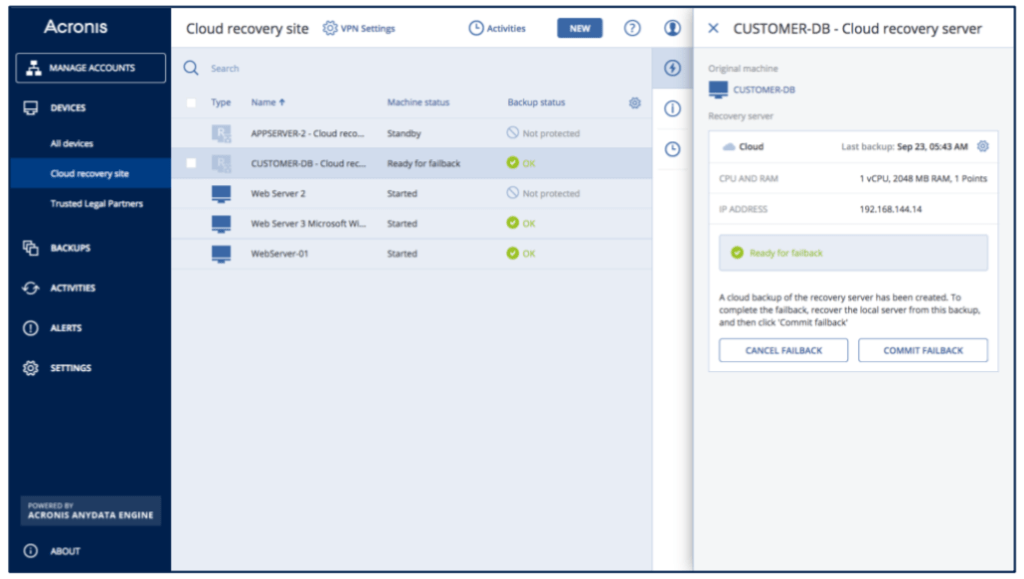
Performing a Failback
♦ Failback is performed manually by an administrator using the cloud recovery server backup
♦ A machine can be restored via a backup agent or by using bootable media
♦ The recovery server is backed up before failback to secure the latest machine state
♦ The recovery server backups are kept intact after the failback procedure
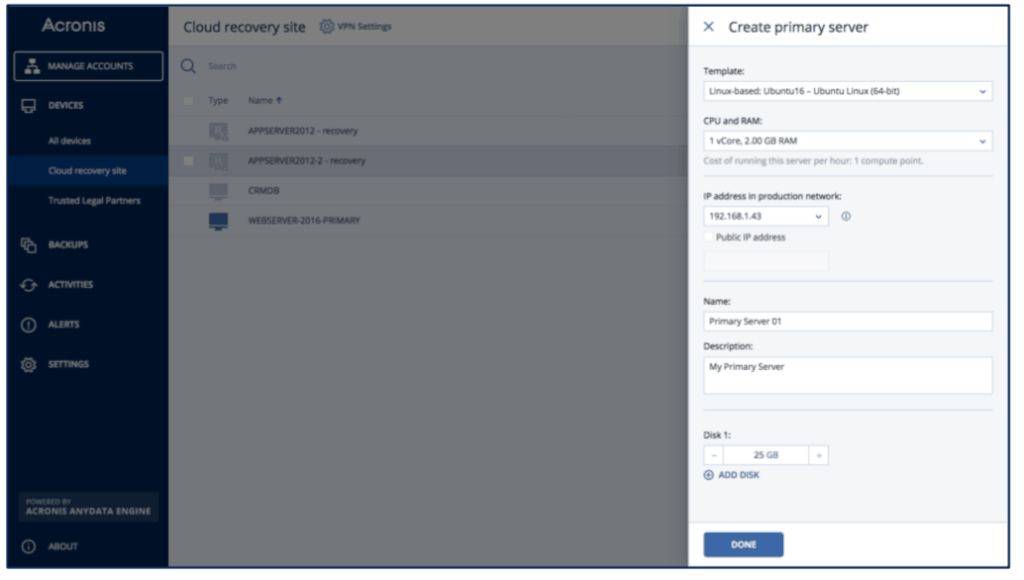
Working with a Primary Server
♦ The primary server is a virtual server, deployed in an Acronis Data Center, and is used to host application nodes or as an additional host when other data protection scenarios are required
♦ The primary server exists only in the cloud and has no counterpart at thecustomer’s site
♦ The primary server is used for application-level protection (SQL Mirror, Exchange DAG, etc.)
♦ It is also suitable for deploying auxiliary appliances like load-balancers, etc.
♦ You can adjust CPU, RAM, and storage
♦ A set of Window or Linux VM templates is available