Estimated reading time: 10 minutes
Social engineering is the term used for a wide range of malicious activities performed through human interactions. It uses psychological manipulation to trick users into making security mistakes or provide sensitive information. Then, with that information, the hacker is able to successfully carry out targeted attacks, such as data theft, a ransomware or a ‘ interruption of services.
Social engineering attacks usually occur in stages . The perpetrator first investigates the intended victim to gather the necessary background information , such as potential entry points and weak security protocols, required to proceed with the attack. Then, the attacker moves to gain the victim’s trust and provide incentives for subsequent actions that violate security practices, such as disclosing sensitive information or granting access to critical resources.
What makes social engineering particularly dangerous is that it relies on human error rather than vulnerabilities in software and operating systems . Mistakes made by legitimate users are much less predictable, making them more difficult to identify and thwart than a malware-based intrusion.

Note that the target of a social engineer is not necessarily a network or software . Being able to enter a building evading security, and then installing a device or stealing documents, are actions that still fall under this type of attack.
The techniques of social engineering
Social engineering attacks come in many different forms and can be carried out wherever human interaction is involved . The following are five most common methods of digital social engineering attacks.
Baiting (from “bait”)
As the name suggests, baiting attacks use a false promise (a decoy , indeed) to whet the victim’s greed or curiosity. They lure users into a trap that steals their personal information or installs malware on their systems.
The most infamous form of baiting uses physical media to disperse malware . For example, attackers leave the bait (typically infected keys) in conspicuous areas where potential victims are certain to see them (e.g. bathrooms, elevators, the parking lot of a targeted company). The decoy has a legitimate look, like a label indicating the content, like the company’s payroll. The clue that reveals what it should contain may change, of course, but has the potential to be potentially very interesting .
Victims pick up the bait out of curiosity and insert it into a work or home computer, resulting in automatic installation of malware on the system.
Lure scams don’t necessarily have to be done in the physical world. Forms of online baiting consist of enticing advertisements leading to malicious sites or encouraging users to download a malware-infected application. Here it leads to the phishing techniques, which we will see shortly.
Defense notes : to defend against these social engineering attacks, as well as paying close attention to what is connected to your computer, it does not hurt to have an efficient antivirus and anti-malware system. For the company, a new generation SIEM system and UEBA help in detect suspicious user behavior and greatly reduce the risk of malware infection.

Scareware (from “to scare”)
Scareware consists of bombarding victims with false alarms and fake threats . Users are tricked into thinking their system is infected with malware, prompting them to install software that has no real benefit (other than the perpetrator) or is malware itself. Scareware is also called deception software ( deception software ), rogue scanner software and fraudware .
A common example of scareware is the legitimate-looking popup banner that appears in your browser as you browse the web , displaying text such as “ Your computer may be infected with spyware programs harmful “. In other cases, the popup offers to install the tool (often infected with malware) for you, or directs you to a malicious site where your computer is infected.
Scareware is also distributed via spam email which distributes bogus warnings, or offers users to buy useless / harmful services. Social engineering is often very imaginative and manages to find ever new ways to deceive. Always be alert.
Defense notes : In case you suspect that the received message is really legitimate, it is best to seek a solution actively , i.e. without using the links suggested by the message same. For example, we received a message from a service announcing that our account has been compromised. If in doubt, you can contact the support of the service directly from their site to ask for clarification. Avoid using the links suggested by the suspicious message at all costs .

Pretexting (from “to pretend”)
In this social engineering attack, an attacker gains information through a series of cleverly constructed lies . The scam is often initiated by an perpetrator who pretends to need sensitive information from a victim in order to perform a critical task.
The attacker usually begins by establishing trust with his victim by impersonating colleagues, police, bank and tax officials, or others who have a right to know authority . The hacker asks questions that are apparently necessary to confirm the victim’s identity, through which he collects important personal data.

Many types of information are collected using this technique, such as identity card numbers, personal addresses and telephone numbers, telephone records, staff vacation dates, bank records, and even security information relating to a physical facility.
Any information, however harmless it may seem, could later be used for a second attack. Even the name of a security guard hired by the company could already be enough to build trust and ask for a tear to the rule when asking for the access code to automatic doors.
Phishing (from “to fish”)
As one of the most popular types of social engineering attacks, phishing scams are email and text message campaigns that aim to create a sense of urgency , curiosity or fear in the victims . Then it prompts them to reveal sensitive information, click links to malicious websites, or open attachments that contain malware.
An example is an email sent to users of an online service notifying them of a policy violation that requires immediate action on their part, such as a mandatory password change. Includes a link to a website, nearly identical in appearance to its legitimate version, which prompts the user to enter their current credentials and new password . After submitting the form, the information is sent to the attacker.
Since identical, or nearly identical, messages are sent to all users in phishing campaigns, detecting and blocking them is much easier for mail servers that have access to threat-sharing platforms.
Defense note : While it is true that in some cases we have become accustomed to not giving weight to these kinds of messages, it is also true that social engineers have become increasingly clever. There is no need to let your guard down. Instead, it is very useful to always be wary of messages that require credentials.
These attacks leverage the fact that it’s easy to fool some users, whether out of distraction or naivety. The best defense is employee training through a ethical phishing service and subsequent targeted training.

Spear phishing (from “spear, and “to fish”)
This is a more targeted version of phishing in which an attacker chooses specific individuals or businesses . They then tailor their messages based on their victims’ characteristics, job positions, and contacts to make their attack less obvious. Spear phishing requires a lot more effort from the author and can take weeks and months to complete. They are much harder to detect and have better success rates when done skillfully.
A spear phishing scenario could involve an attacker who, impersonating an organization’s IT consultant, sends an email to one or more employees. It is worded and signed exactly as the consultant normally does, thus fooling recipients into thinking it is an authentic message. The message prompts recipients to change their password and provides them with a link that redirects them to a malicious page where the attacker now captures their credentials.

How to defend against social engineering attacks
Social engineers manipulate human feelings, such as curiosity or fear, to carry out patterns and lure victims into their traps. Therefore, it is essential to be cautious whenever you feel alarmed by an email, attracted to an offer displayed on a website, or when you come across digital media wandering around. Being alert can help protect you from most social engineering attacks that happen online.
Additionally, the following tips can help you improve your vigilance in relation to social engineering attacks.
- Do not open emails and attachments from suspicious sources . If you don’t know the sender in question, you don’t need to reply to an email. Even if you know them and are suspicious of their message, cross-check and confirm the news from other sources , such as over the phone or directly from a service provider’s website. Even an email that appears to come from a trusted source may have been initiated by an attacker.
- Use multi-factor authentication . One of the most valuable pieces of information attackers look for is your user credentials . Using 2-factor authentication helps ensure the protection of your account in case of system compromise. There are free applications for all types of mobile devices that allow you to implement this type of authentication.
- Be wary of attractive offers . If an offer seems too tempting , think twice before accepting it as real. Use Google to check the topic and quickly determine if you are dealing with a legitimate offer or a trap.
- Update your antivirus / antimalware software . Make sure automatic updates are turned on. Check periodically that updates have been applied and scan your system for possible infections.
If your company has an IT department, these recommendations should be standard security measures.

Security services for companies
When you think about the data that your company holds and manages, you are never too cautious in defense. Social engineering relies on the fact that an employee hacks more easily than a computer , which is often true.
In addition to the cyber protection measures listed above, it is good that all employees are aware of the risks and potential threats.
SOD offers a series of services that go in this direction. The first and perhaps most important is ethical phishing in which we try to attack the company with phishing techniques . We find out what the weak points are and organize internal training to provide the right tools for staff.
We also have the classic Vulnerability Assessment and Penetration Test for testing cybersecurity systems. Addons are applicable to this service to cover a greater number of areas. There is a specific addon for app analysis and code review , but also one where we try to hack the company with physical attacks . We will test the physical security of the company, the ability to enter buildings, access to network controllers and more.
Finally, to keep networks under control, the SOCaaS service allows you to monitor the entire network, identify suspicious actions (with behavior analysis via artificial intelligence), unauthorized installations, breach attempts and much more.
Data security in the company is really important, contact us to find out how we can help you!
Useful links:

PHP is one of the most popular scripting languages on the web today. According to W3Techs, PHP is used by over 82% of all websites that use a server-side programming language. This means that 8 out of 10 sites use PHP in one form or another. Being a scripting language, it is essential to update PHP to the latest version available, unless you have special needs.
Today we try to understand the importance of updating to the latest PHP versions, not only for security reasons, but also to improve performance and support. The precise procedure will also be shown via a simple how-to.
When to update PHP?
As with any software, PHP has a lifecycle that it must adhere to in order to continue making improvements and moving forward in development. Each major PHP release is generally fully supported for two years. During this time, bugs and security issues are regularly fixed and fixed. a third year of support is guaranteed, only for what concerns language security and not performance.
PHP versions supported
As of today (summer 2020), anyone running a version of PHP 7.1 or lower no longer benefits from security support and is exposed to vulnerabilities that will not be fixed. According to the official WordPress Stats page, at the time of writing this article, over 41% of WordPress users are still using PHP 7.1 or lower. This is not only a security issue, but it is also a hindrance as there are still many sites that do not take advantage of the further performance improvements introduced with PHP 7.2 and later.
Unfortunately, not everyone is aware of the danger and since updating PHP is an operation that must be done on the server and not from the site itself, a good portion of users do not even know how to proceed.
 As can be seen from this image, the currently supported versions of PHP are 3: 7.2, whose security support will end on November 30, 2020; 7.3, supported until December 2021 and 7.4 supported until November 2022. Warning: in the last 12 months of the version’s life, the only guaranteed support is the security one.
As can be seen from this image, the currently supported versions of PHP are 3: 7.2, whose security support will end on November 30, 2020; 7.3, supported until December 2021 and 7.4 supported until November 2022. Warning: in the last 12 months of the version’s life, the only guaranteed support is the security one.
Slow updates
There are many factors that could affect a slow adoption of recent versions of the language, here are some of them:
1. The owners of the sites, not being technicians, do not know the language and do not know they have to update PHP in order to have a safe and up-to-date site.
2. Those who use custom themes or plugins on their site want to be sure that the new PHP versions do not have backwards compatibility problems. These developers are waiting for the new guidelines to be released for the most recent versions, and only after checking their plugins and themes do they fully adopt the new version.
3. Some hosts are afraid to update the language on the server as it could lead to a wave of support tickets. Luckily, providers increasingly make the choice of version available to the end user, as we will see shortly.
Honestly, I don’t understand all this fear of updating PHP and keeping your systems running well and safe. I think the wait is quite useless and risky.
How to update PHP on SOD hosting panel
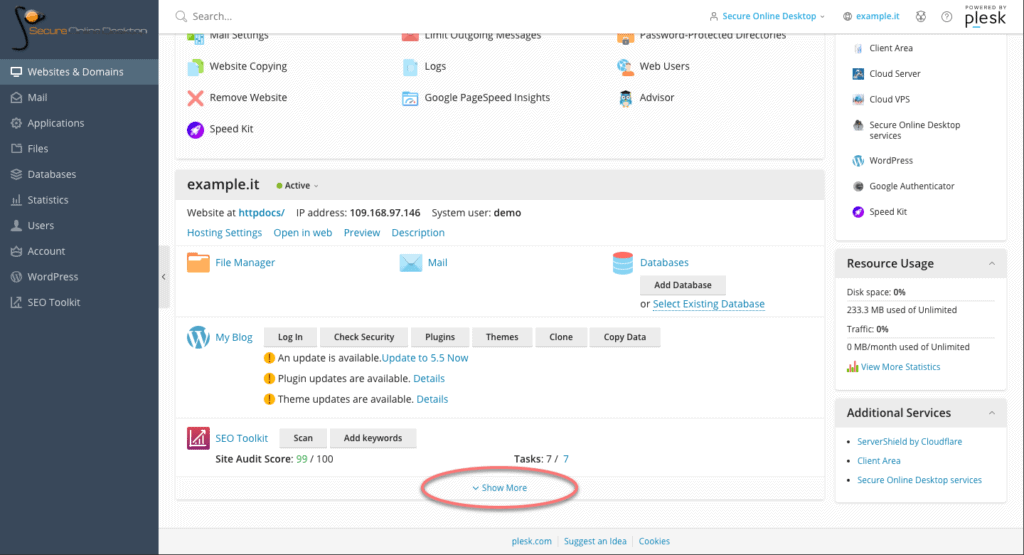
First, log into your control panel and from the main dashboard, scroll down to the section of the site concerned. At the bottom, click on the “Show More” button to view hosting options.
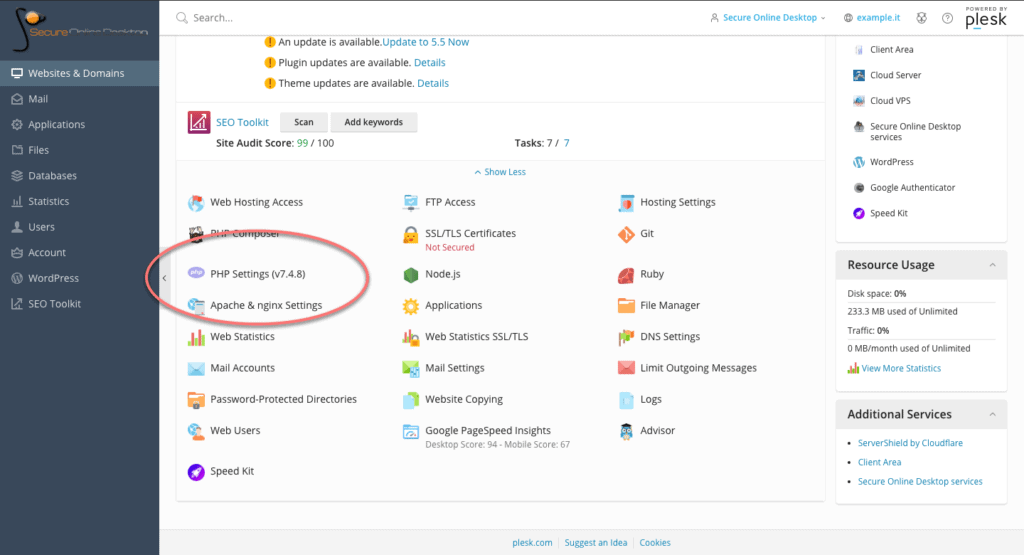
Among the options, look for the one called “PHP Settings”. Note that the version currently in use by the server is already shown next to the name. Click on the option to land on the PHP settings page.
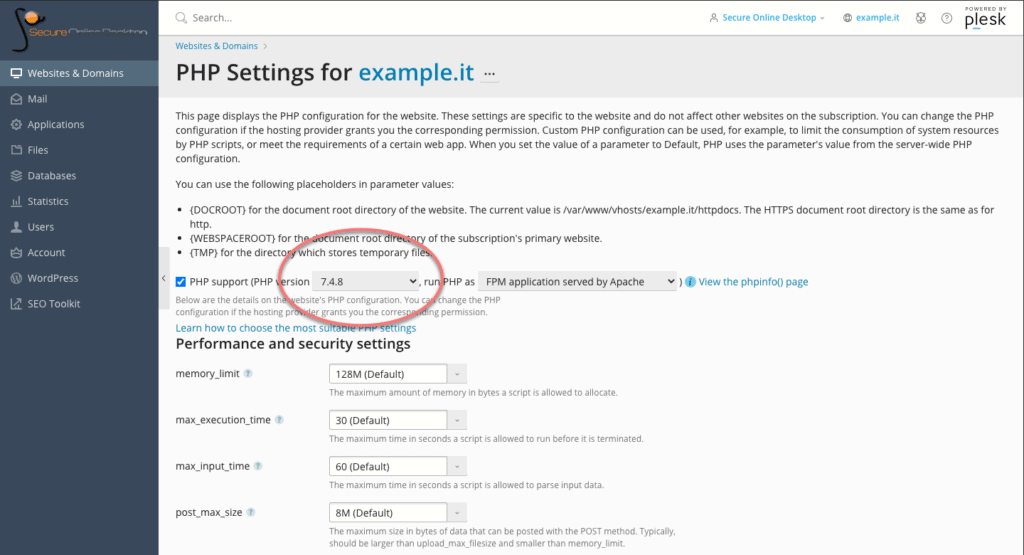
Within the PHP section, it is possible, through a drop-down menu, to change the version in use. Versions that are no longer updated are marked as “outdated”, but still selectable.
On the page, in addition to the version active on the server, it is possible to modify many other PHP options relating to performance and security. For example the limit of the dedicated memory, the maximum execution time of the scripts, the location of the scripting folders and so on.
These are all features that the average user does not need on a daily basis, but the fact that such in-depth control of PHP options is available is a plus for the flexibility of the control panel and service.
Make sure your host is using the latest versions of PHP
As we have seen, updating PHP to the supported version is a simple operation to be performed through the appropriate panel of the hosting plan.
A few years ago, a great article titled “Whipping Your Host Into Shape” by Joost de Valk went into detail about how the real problem is that providers don’t adopt recent versions faster and, even if they do, they don’t encourage users to update themselves. Years have passed since that article and I hope that the trend will improve, and that more and more people think about the security of their portals also through the updating of the infrastructure that hosts them.
Through the control panel of SOD hosting plans, keeping the service updated and secure is simple, and updating PHP is just an example of the potential of the panel itself. Check for yourself by accessing a demo of the service.
[btnsx id=”2931″]
Useful links:
Manage WordPress from the hosting panel

Let’s Encrypt is a free, automated and open Certification Authority. The objective of Let’s Encrypt and the ACME protocol is to make it possible to set up an HTTPS server and have it automatically obtain a browser-trusted certificate, without any human intervention. This is accomplished by running a certificate management agent on the web server.
With our Webhosting service based on Plesk technology you can have free SSL certificates with Let’s Encrypt so all your web pages will be secured.
Plesk plugin is installed by default on all subscriptions, you just need to enable it if you like to use SSL certificate to protect your web site.
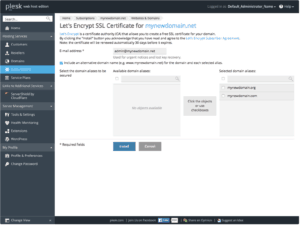
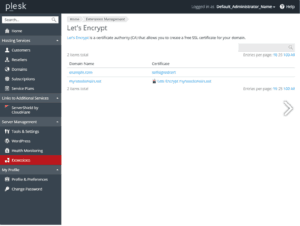
Creating SSL Certificates with Let’s Encrypt
To create your SSL Certificate just logon in your Webhosting portal, click on domain you like to create SSL certificates then click on related icon like show below:
If you still don’t have a Webhosting service you can access to Webhosting demo.
Screenshots
HTTPS and SEO
Once again Google dictates the rules to comply with so as not to see its site “penalized” compared to others. We are not talking about the classic penalties already explained in this section .. but we can talk about “positioning factor” as evidenced by one of the first statements provided by Google in 2014: “Https as a positioning factor”.
Starting from January 2017, to help users browse the web safely, Google Chrome will indicate as “NOT SECURE” all those pages that collect passwords or credit cards.
Unlike other positioning factors, implementing an SSL certificate involves difficulties, risks and costs.
[btnsx id=”2931″]
Useful links:
CloudFlare free Plesk extension for Webhosting users
Customers
Twitter FEED
Recent activity
-
SecureOnlineDesktop
Estimated reading time: 6 minutes L'impatto crescente delle minacce informatiche, su sistemi operativi privati op… https://t.co/FimxTS4o9G
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The growing impact of cyber threats, on private or corporate operating systems… https://t.co/y6G6RYA9n1
-
SecureOnlineDesktop
Tempo di lettura stimato: 6 minuti Today we are talking about the CTI update of our services. Data security is… https://t.co/YAZkn7iFqa
-
SecureOnlineDesktop
Estimated reading time: 6 minutes Il tema della sicurezza delle informazioni è di grande attualità in questo peri… https://t.co/tfve5Kzr09
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The issue of information security is very topical in this historical period ch… https://t.co/TP8gvdRcrF
Newsletter
{subscription_form_1}© 2023 Secure Online Desktop s.r.l. All Rights Reserved. Registered Office: via dell'Annunciata 27 – 20121 Milan (MI), Operational Office: via statuto 3 - 42121 Reggio Emilia (RE) – PEC [email protected] Tax code and VAT number 07485920966 – R.E.A. MI-1962358 Privacy Policy - ISO Certifications