 Piergiorgio Venuti
Piergiorgio Venuti
Two Factor Authentication
Two Factor Authentication
Protect your Client Area with Two Factor Authentication via Google Authenticator
Now you can protect your Client Area login with Google Authenticator so you will add and extra layer of security on your Cloud Account.
Two Factor Authentication
How to enable Google Authenticator on Secure Online Desktop account
1 Access to your Client Area and log in with your account;
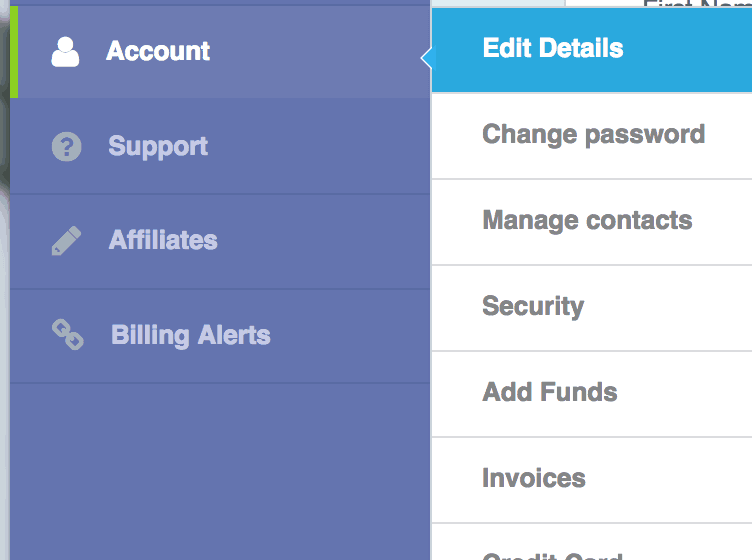
2 Go on Account -> Edit Details section;
3 Flag “Two-Factor Authentication” option;

4 Scan the generated code with your Google Authenticator app (download it from Apple Store or Google Play) for your smartphone;
5 Save your settings;
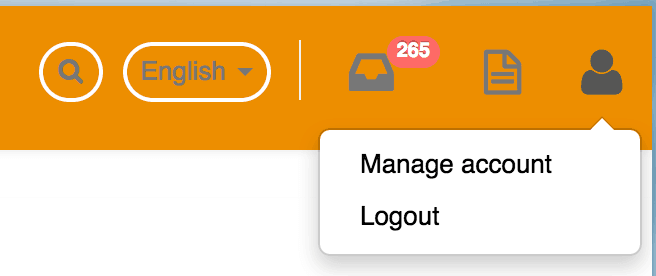
6 Logoff from your account and login again;
7 At this point, after username and password you need to insert the OTP code generated from you Google Authenticator app.
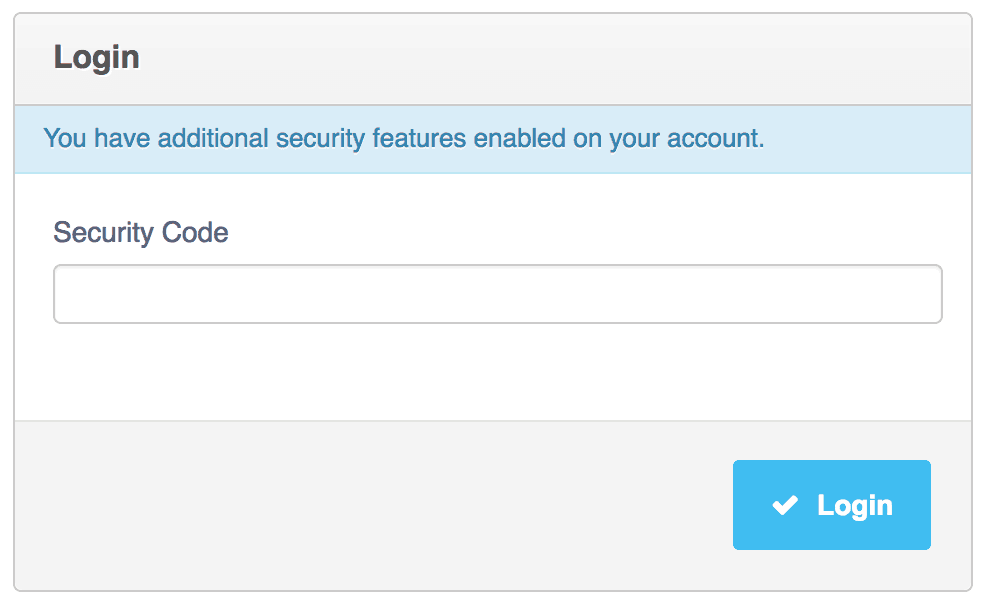
Now that you are done your Cloud Account and all related Cloud Services are safer because and attacker need to not just username/password but also your OTP code. You can disable this feature any time in your Account Details.
Customers
Twitter FEED
Recent activity
-
SecureOnlineDesktop
Estimated reading time: 6 minutes L'impatto crescente delle minacce informatiche, su sistemi operativi privati op… https://t.co/FimxTS4o9G
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The growing impact of cyber threats, on private or corporate operating systems… https://t.co/y6G6RYA9n1
-
SecureOnlineDesktop
Tempo di lettura stimato: 6 minuti Today we are talking about the CTI update of our services. Data security is… https://t.co/YAZkn7iFqa
-
SecureOnlineDesktop
Estimated reading time: 6 minutes Il tema della sicurezza delle informazioni è di grande attualità in questo peri… https://t.co/tfve5Kzr09
-
SecureOnlineDesktop
Estimated reading time: 6 minutes The issue of information security is very topical in this historical period ch… https://t.co/TP8gvdRcrF
Newsletter
{subscription_form_1}© 2023 Secure Online Desktop s.r.l. All Rights Reserved. Registered Office: via dell'Annunciata 27 – 20121 Milan (MI), Operational Office: via statuto 3 - 42121 Reggio Emilia (RE) – PEC [email protected] Tax code and VAT number 07485920966 – R.E.A. MI-1962358 Privacy Policy - ISO Certifications












